What are The Types of Dashboards in a SIEM Solution?
Dashboards are an integral component of any effective SIEM solution. After log data is aggregated from different sources, a SIEM solution prepares the data for analysis after normalization. The outcomes of this analysis are presented in the form of actionable insights through dashboards. Many SIEM solutions come with pre-configured dashboards to simplify the onboarding process for your team. Besides, an ideal solution should also allow an organization to customize dashboards as per its requirements. In this article, we discuss various types of dashboards available on Logsign SIEM.
(You can also check our article about The step-by-step procedure to customize a dashboard on Logsign SIEM )
On Logsign SIEM, more than 40 types of dashboards are available. These dashboards are categorized into a total of 11 categories as follows:
If you are using Logsign for the first time or have not changed the default dashboard, the Welcome dashboard is the default dashboard on Logsign SIEM. The default dashboard contains an all event-time histogram, along with event context, event types, and event actions.
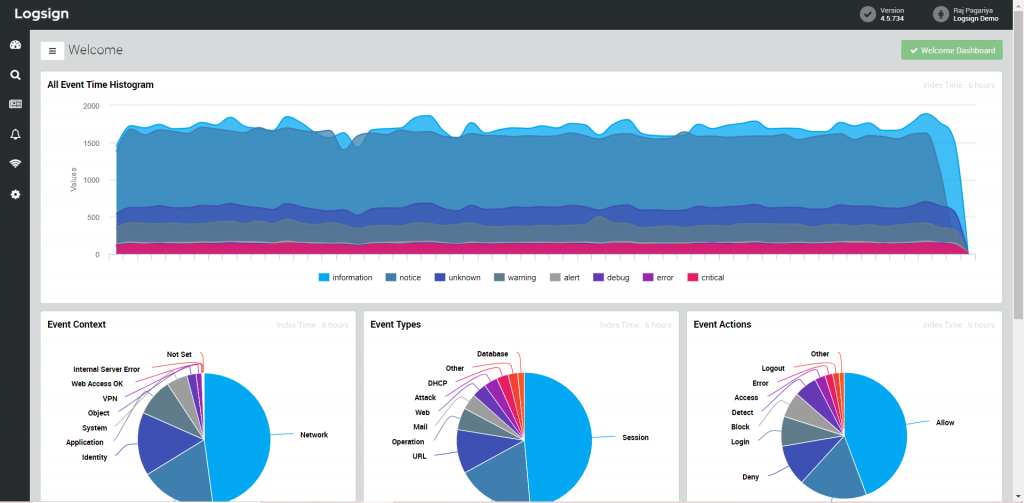
Figure 1: Welcome dashboard (default dashboard on Logsign SIEM)
Depending on your requirements and job profile, you can set any dashboard as the default dashboard so that it appears on the landing page after you login. Further, a user can add, modify, or remove widgets on these dashboards through “Add a widget” option. For every widget, Logsign SIEM has allocated a default time index. A user can configure this time index from a duration as short as 1 hour to as long as 365 days.
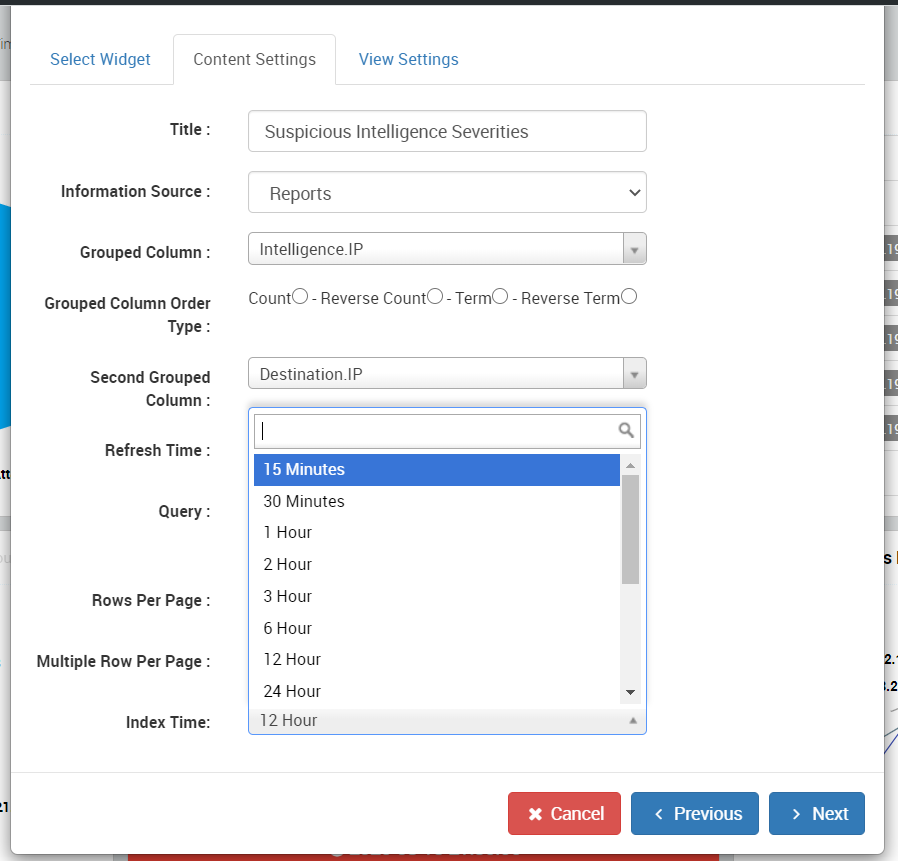
Figure 2: Updating the time index for a widget
This category has two dashboards at present. It provides information about the classification of threat messages, external malicious source and destination IP addresses, suspicious intelligence severities, most active threat sources/destinations, time analysis, and malicious activity counts.
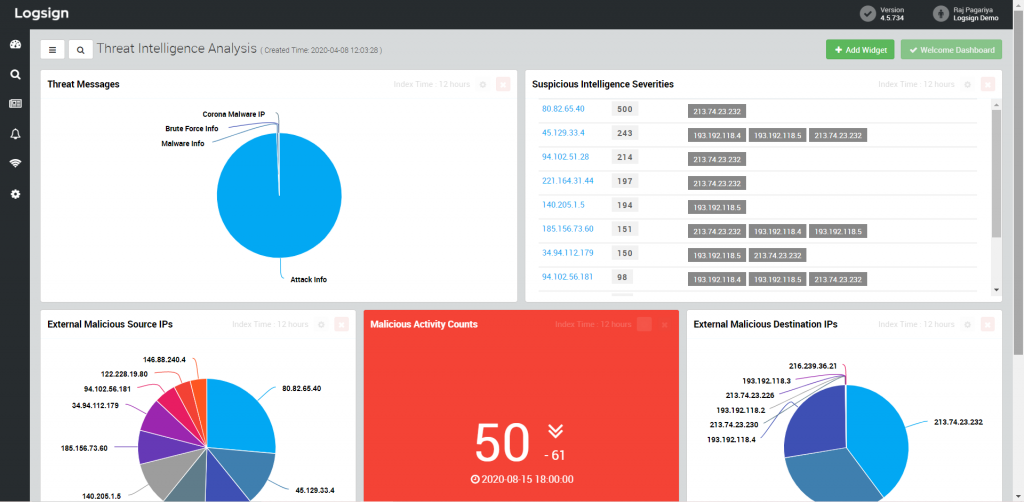
Figure 3: Threat Intelligence Analysis dashboard on Logsign SIEM
This category has six dashboards: Attack Analysis, Endpoint Analysis, Security Overview, IDS, Content Filtering Analysis, and Trend Micro.
Dashboard
Information widgets
Attack Analysis
Attack activity by internal/external source IP addresses, destination ports, source interface, source countries, and timeline
Endpoint Analysis
Infected sources, threat details, detected virus, and endpoint security events
Security Overview
Security activities, risk by event sources, risk summary by severity, risk summary by source/destination country, along with detected activities for attacks, malware, virus, and spam
IDS
Attack histogram, attack by source/destination IP addresses, destination/source attack map, and external/internal IP attack severity
Content Filtering Analysis
Allowed/blocked domain access, allowed/blocked categories, allowed/blocked URL sources, and URL categories
Trend Micro
TrendMicro products, event map info, event types, event activities, event subtypes, among other event-related information
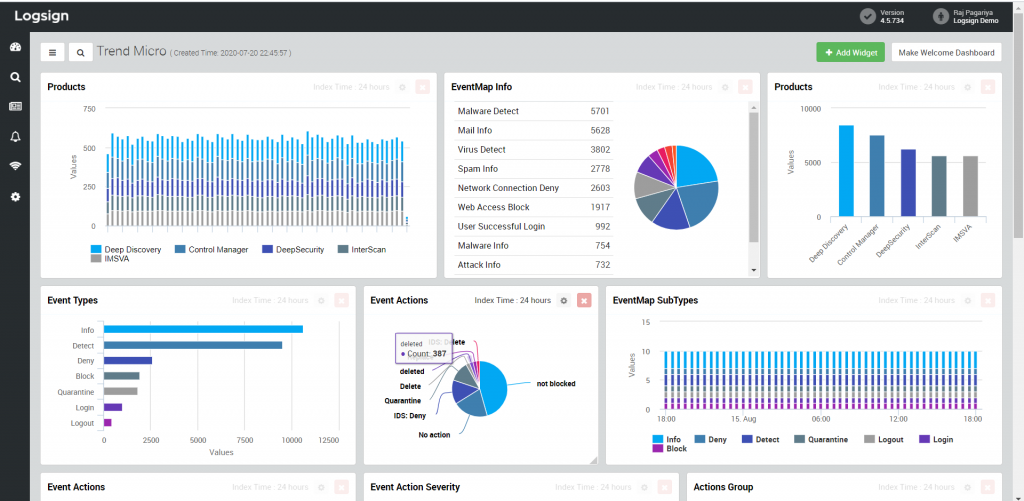
Figure 4: TrendMicro dashboard on Logsign SIEM
This category has a total of eight dashboards. These dashboards visualize information about various facets of your organization’s network.
Dashboard
Information widgets
FTP Analysis
FTP time analysis and top sources/destinations
UDP Analysis
UDP time analysis, top sources/destinations, top source/destination country, and destination ports
Protocol Center
Usage by protocol timeline, top connection sources, port usage, and outbound/inbound connections by destination ports
Traffic Awareness
Traffic anomaly time analysis, traffic anomaly sources, and critical source/destination country
Traffic Overview
Traffic analysis, source/destination country, top source/destination country, and traffic analysis from source IP to unique destination IPs
HTTP/S Analysis
Blocked/allowed HTTP/S requests, top sources/destinations, and time analysis
DNS Analysis
DNS time analysis and top sources/destinations
Bandwidth Analysis
Bandwidth (download/upload) usage, download/upload MB usage, and download usage for TCP and UDP
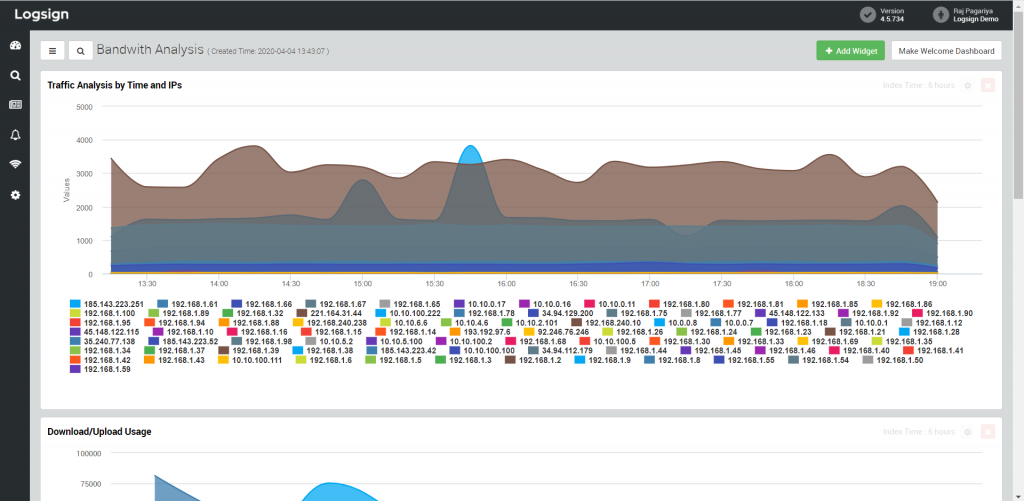
Figure 5: Bandwidth Analysis dashboard on Logsign SIEM
This category has five pre-configured dashboards concerning alerts and actions objects.
Dashboard
Information widgets
Warning Level Alerts
Alert details, unique counts by action object, total count, and information level alerts
Critical/Emergency Level Alerts
Alert details, unique counts by action object, and total count
Compliance Alerts & Use Cases
Under development
Action Objects & Alert Overview
Information/warning/critical/emergency level alert counts, suspicious users, suspicious internal/external hosts, suspicious objects and alerts
Alert Rules Overview
Suspicious objects time analysis with unique alert counts, alerts time analysis with unique object counts, alerts & action object analysis

Figure 6: Alert Rules dashboard on Logsign SIEM
This category consists of pre-configured dashboards focusing on various servers inside an organization such as web, FTP, mail, DHCP, and DNS.
Dashboard
Information widgets
Web Server
Event timeline, external IP addresses, result codes, source country, URL paths, data sources, and messages
FTP Server
Usage timeline, top source IP addresses, server messages, source users, and event actions
Mail Server
Event timeline, top mail receivers/senders, mail events, server messages, and mail subjects
DHCP Server
Timeline, server messages, top source IP addresses, top MAC addresses, and data sources
DNS Server
Time analysis, server messages, top source IP addresses, server actions, and DNS request sources
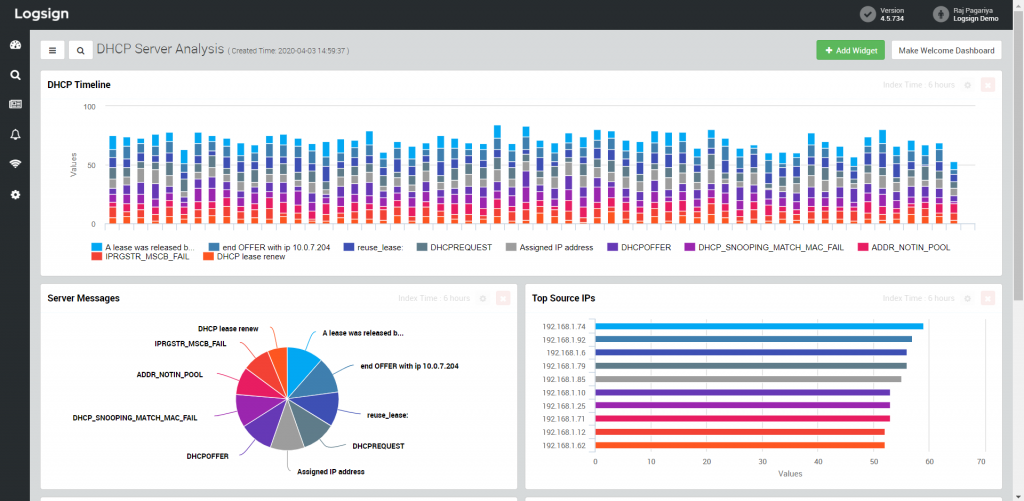
Figure 7: DHCP Server Analysis dashboard on Logsign SIEM
This category focusses on system events inside your organization’s technical infrastructure. It provides six pre-configured dashboards for your security team.
Dashboard
Information widgets
Network Layer System Events
Activity and their details, event messages, and events with severity
System Overview
System categories, information messages, system activity by event sources, and system error messages
Application Layer System Events
Activities, messages, system errors, and message details
Critical System Events
Time analysis, critical events, critical event count, and critical devices
SIEM System Events
CPU utilization, disk utilization, EPS stats, and health check critical/last states
Security Layer System Events
Activities, messages, system errors, and message details
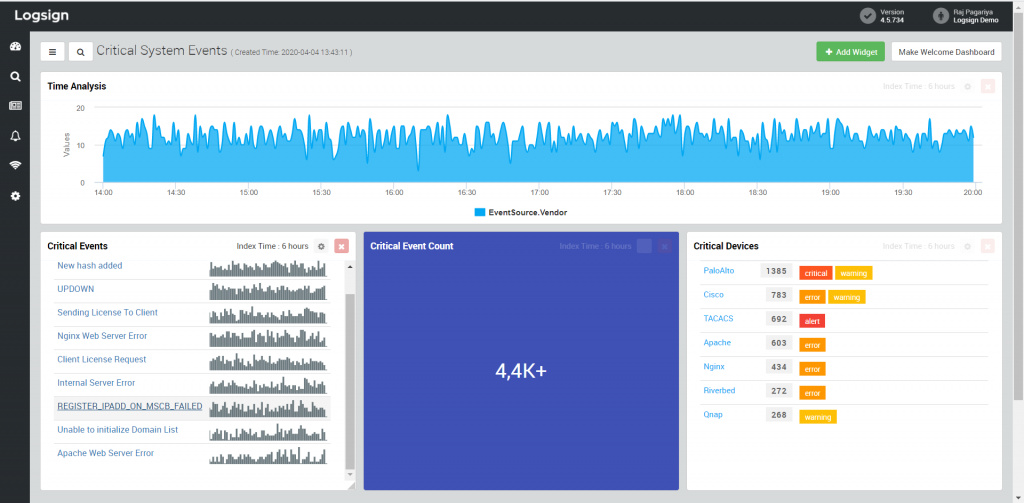
Figure 8: Critical System Events dashboard on Logsign SIEM
Dashboards in this category provide detailed information about security events in your technical infrastructure based on their severity and mapping inside Logsign SIEM.
Dashboard
Information widgets
Severity
Event timeline, context, type, subtype, data sources, and details
Mapping
Classification (identity/security/object/network/system/application), context, type, and subtype
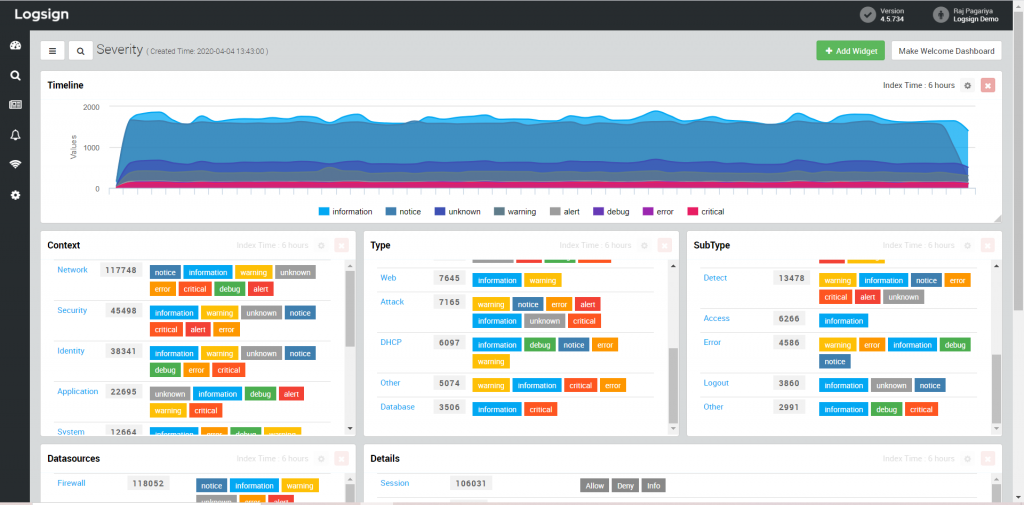
Figure 9: Event Severity dashboard on Logsign SIEM
This category of dashboards provides information about guest users who connected to your organization’s wireless network.
Dashboard
Information widgets
Hotspot User Count Analysis
Logon/Logout user count, online/registered user count, login failed user count, location-based analysis for logon, login failed, registered users, and logout
Hotspot User Data Usage Analysis
Users upload/download MB usage and location-based data usage
Hotspot User Activity Analysis
Logon/logout user activity, login failed users, login failed user activity and reasons, account termination, and all user messages
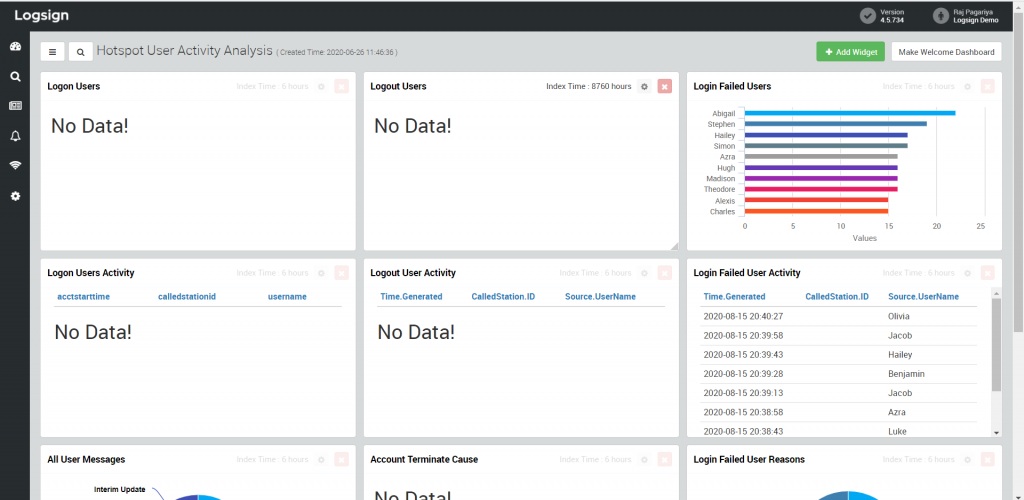
Figure 10: Hotspot User Activity Analysis dashboard on Logsign SIEM
Figure 9 shows no data as we have disabled connections to the wireless network in our demo environment.
This category gives insights into your organization’s databases. It has three dashboards: one gives a general overview while one each is dedicated for MSSQL and Oracle.
Dashboard
Information widgets
Database Overview
Usage timeline, data sources, and actions
MSSQL
Usage timeline, object name and database name, general events, type and actions, and activity details
Oracle
Usage timeline, object name, messages, SQL commands
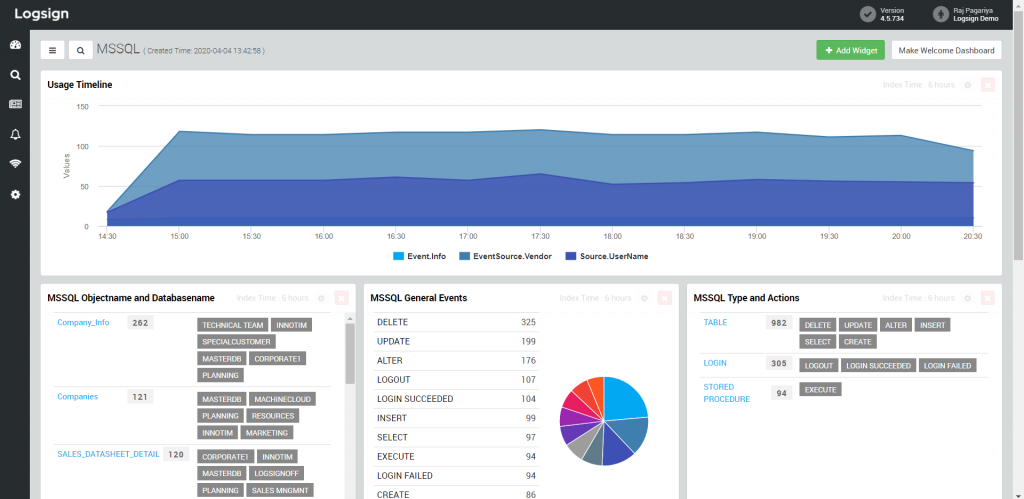
Figure 11: MSSQL dashboard on Logsign SIEM
This category of dashboards illustrates information about user account management, user identity management, and VPN-based user activities.
Dashboard
Information widgets
VPN User Overview
Logon activity counts, logon failure counts, top users for logon attempts/failures, activity details, time analysis, and login/failure by countries
Account Management
Activities count, top 10 activities, created/deleted users, enable/disable users, lock/unlock users, messages, password change activities, and expired password by account
Identity Overview
Logon activity counts, logon failure counts, top users for logon attempts/failures, logon and logon failure by source IP address, and logout activity by users
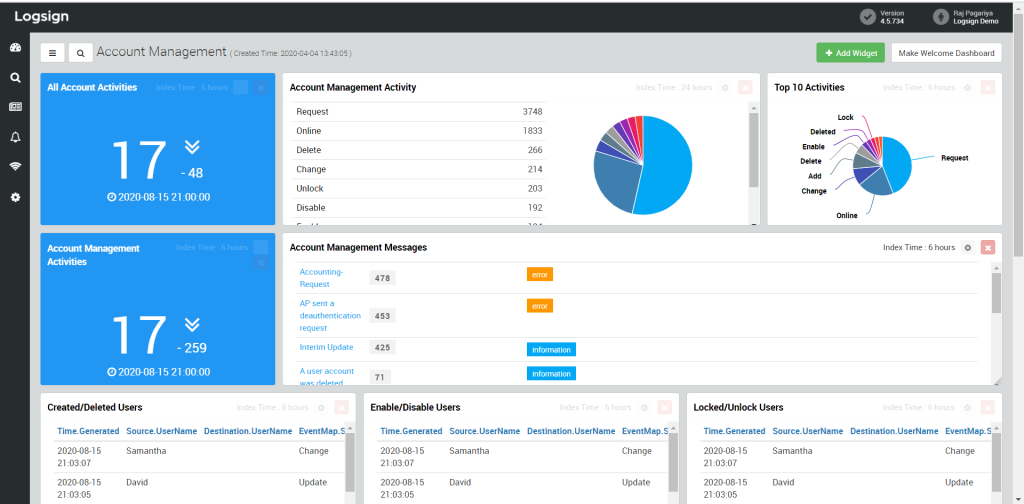
Figure 12: Account Management dashboard on Logsign SIEM
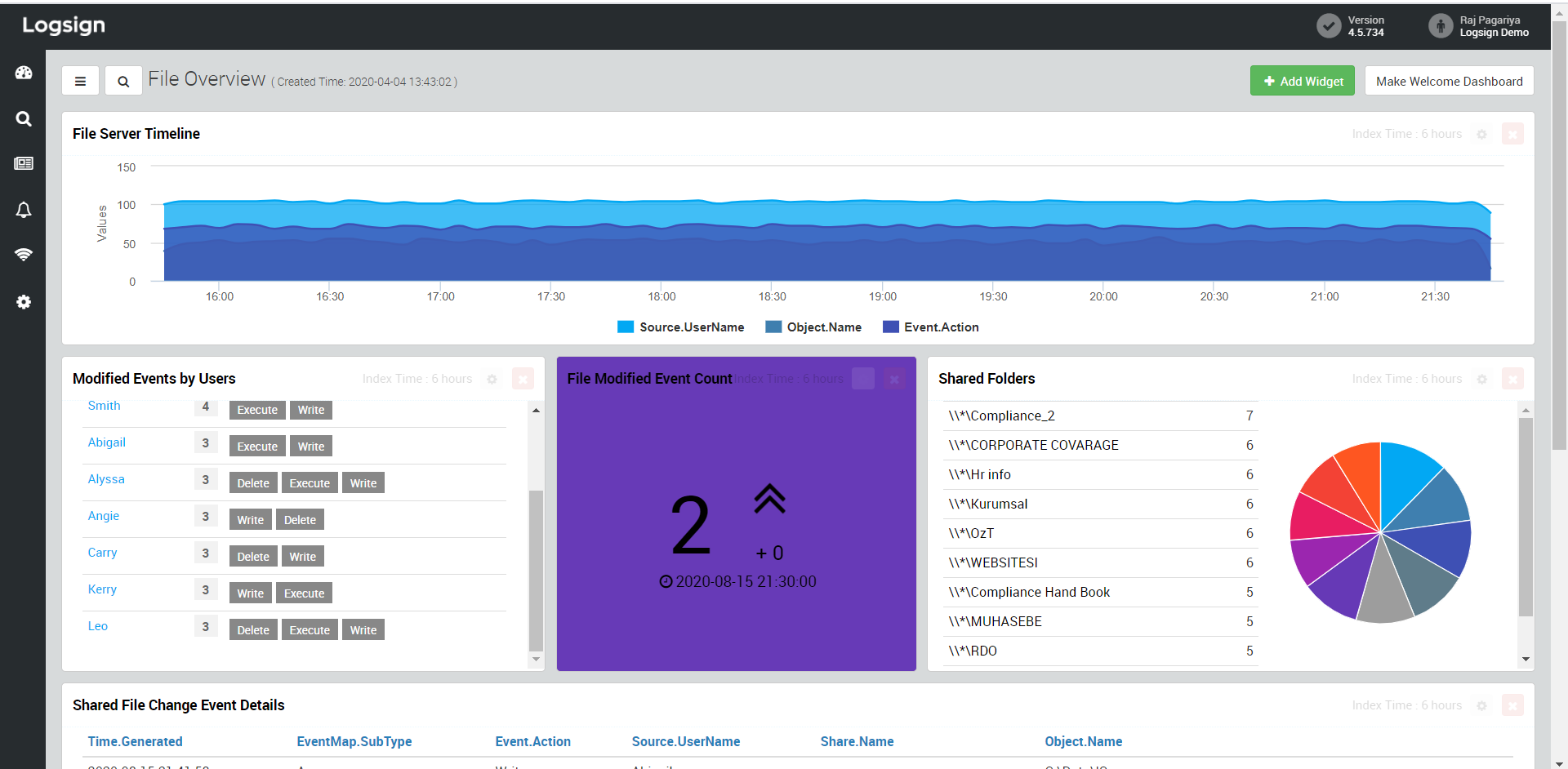
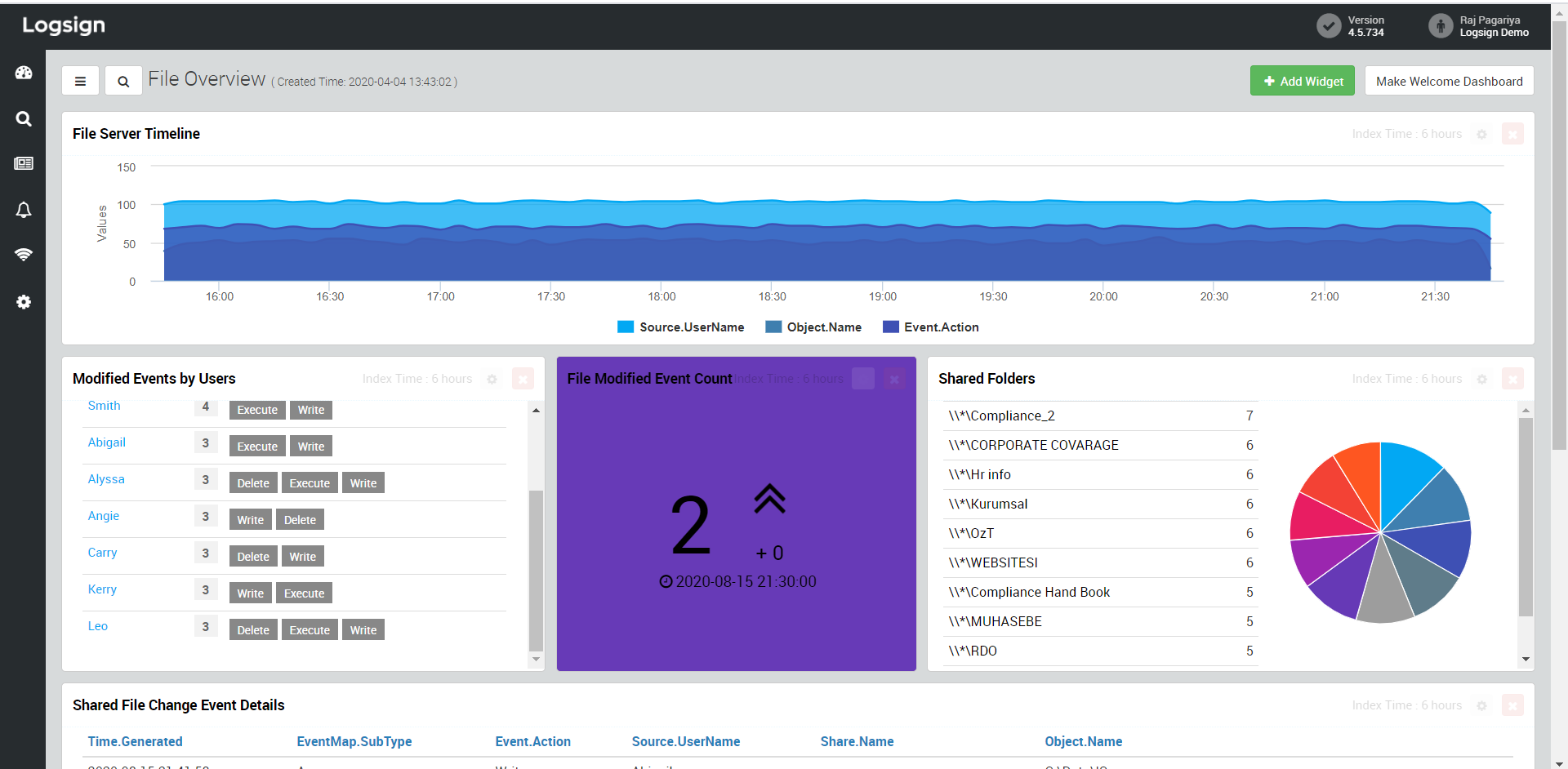
This category of dashboards presents visualized information about the file system of your organization. It covers user activities, file share events, and detailed insights on change events.
Dashboard
Information widgets
File Shared
Time analysis, shared folders, shared file events, and event details
File System
Time analysis, actions, user file activity, and object names
File Overview
File server timeline, shared folders, file modified event count, modified events by users, and shared file change event details
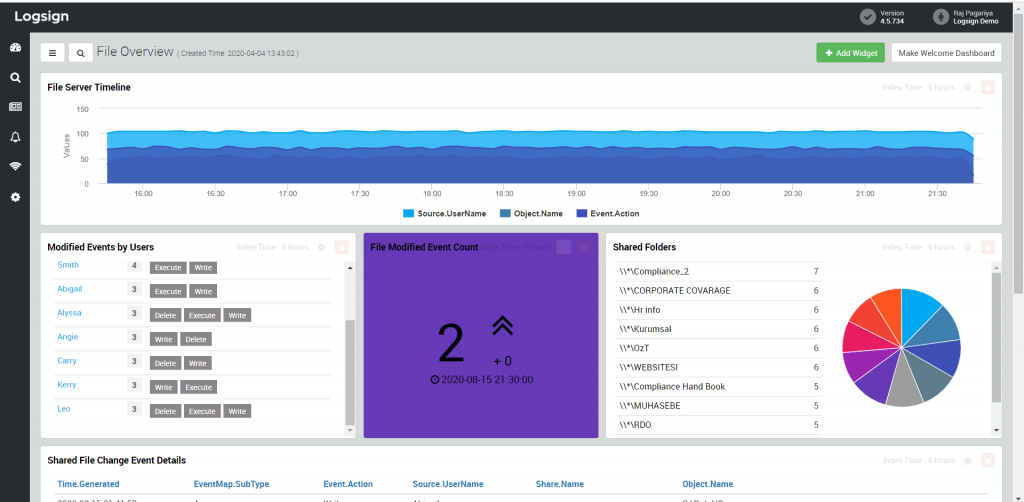
Figure 13: File Overview dashboard on Logsign SIEM
Have you been able to utilize these dashboards for your organization? Feel free to get in touch with our Support team if you have any questions or queries.