What are the Types of Reports on a SIEM Solution?
A Security Information and Event Management (SIEM) solution collects log data from numerous sources within your technical infrastructure. This acquisition and normalization of data at one single point facilitate centralized log management. It allows businesses to generate reports containing security information about their entire IT infrastructure. Reporting, out of many benefits of a SIEM solution, also helps businesses in fulfilling their documentation and compliance requirements. In this article, we explore various types of reports on a SIEM solution.
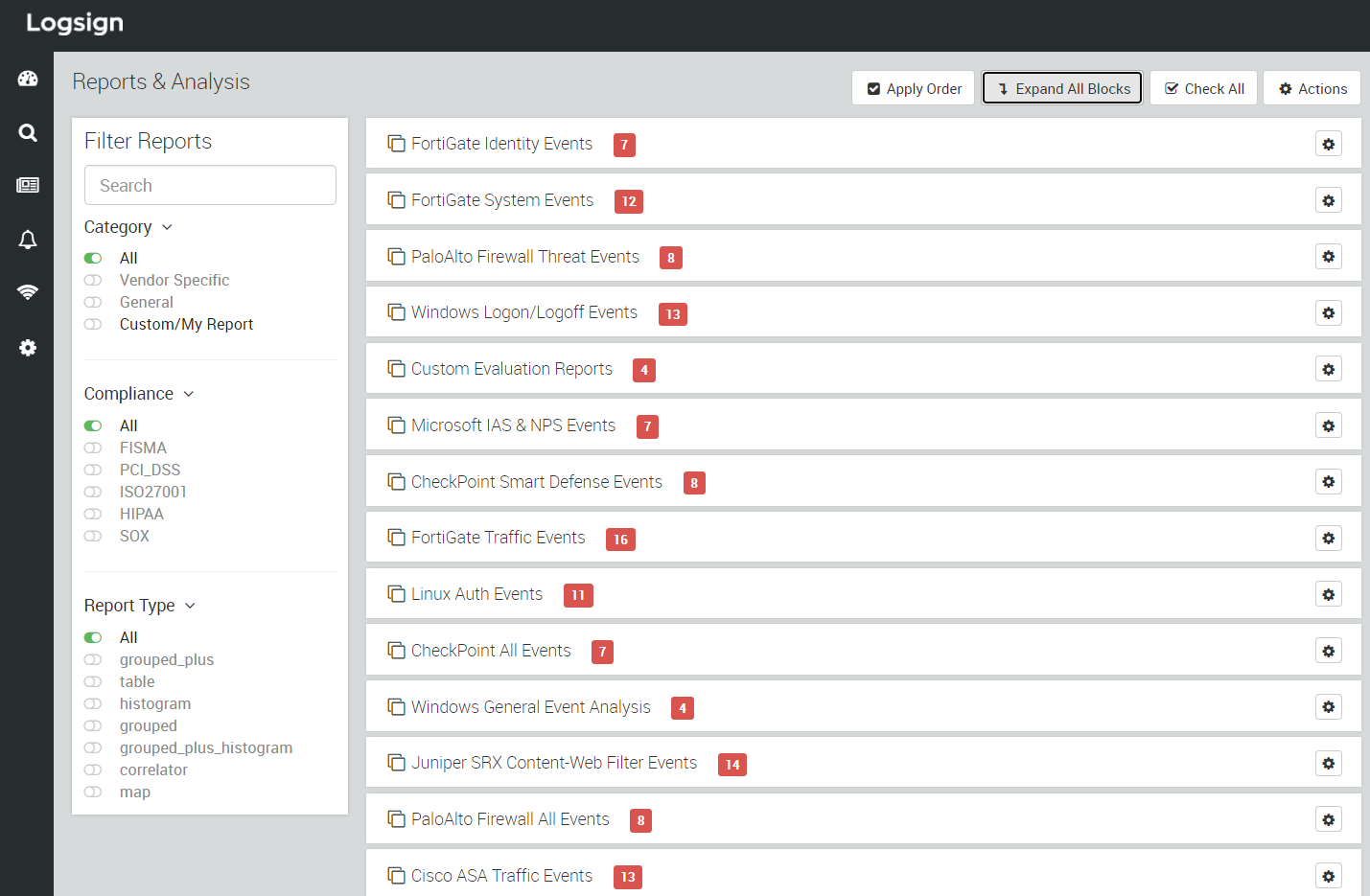
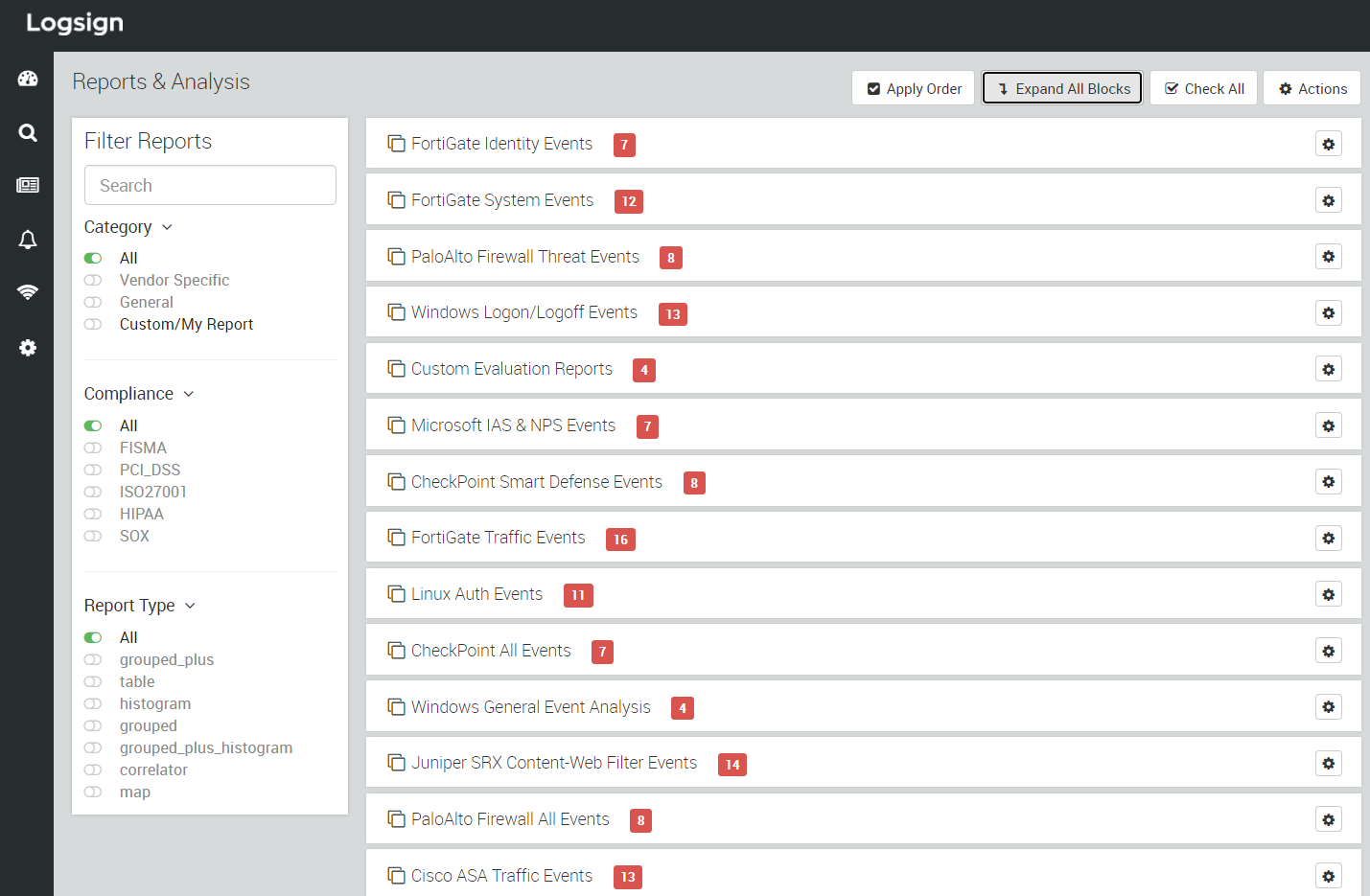
Reports are arranged into different blocks in the Reports & Analysis section on Logsign SIEM. There are more than 140 pre-configured reports for your security team to utilize and explore. You can also schedule these reports to be delivered on your email address (we will discuss this in one of our upcoming articles).
These reports are grouped into various blocks. While you can browse them block-wise, you can also use filter options available for category, compliance, and report type.
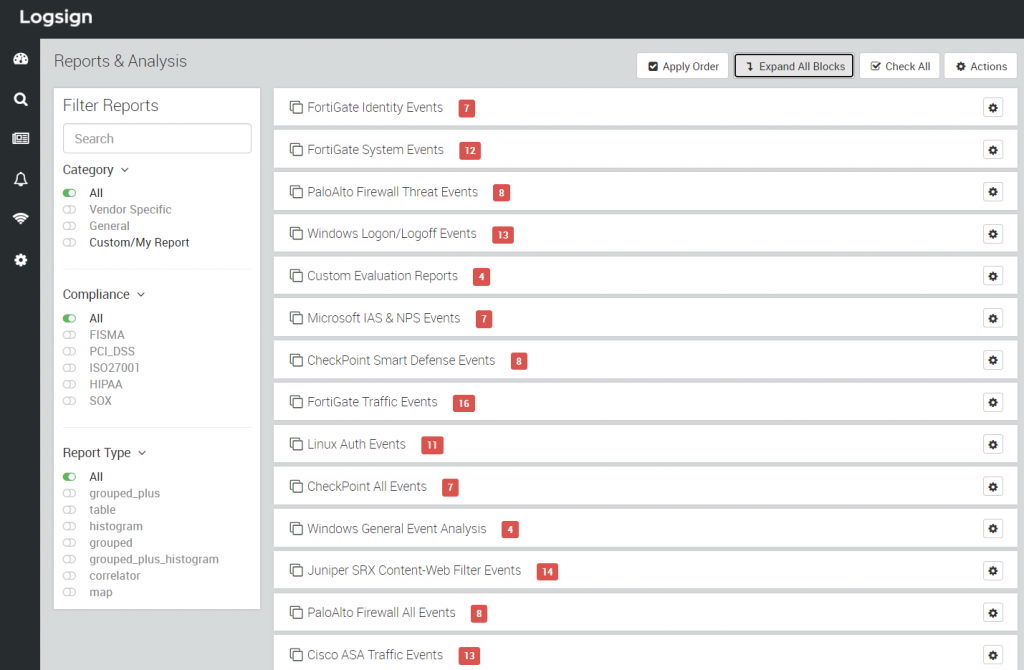
Figure 1: Reports & Analysis on Logsign SIEM
To further simplify the various types of reports available on Logsign SIEM, we have prepared the following table.
Group
Block name
Fortigate
Fortigate Identity Events
Fortigate System Events
Fortigate Traffic Events
Fortigate Antivirus Events
Fortigate VPN Events
Fortigate Attack Events
Fortigate Content Web Filter Events
Fortigate General Events
Palo Alto
Palo Alto Firewall Threat Events
Palo Alto Firewall All Events
Palo Alto Firewall Content Filter Events
Palo Alto VPN Events
Palo Alto Firewall Traffic Events
Windows
Windows Logon/Logoff Events
Windows General Event Analysis
Windows Account Logon
Windows System Events
Windows Account Management Events
Windows Directory Service Events
Windows File Activity Events
Windows Server All Security Auditing Events
Windows File Share Events
Microsoft
Microsoft IAS & NPS Events
Microsoft DHCP Events
Microsoft Exchange 2007 Events
Microsoft Exchange 2003 Events
Microsoft IIS Web Server Events
Microsoft Exchange 2016 Events
Check Point
Check Point Smart Defense Events
Check Point All Events
Check Point Firewall Traffic Events
Check Point Identity Events
Check Point Application Control Events
Check Point Antivirus Events
Linux
Linux Auth Events
Linux DHCP Events
Juniper
Juniper SRX Content-Web Filter Events
Cisco
Cisco ASA Traffic Events
Cisco ASA All Events
Cisco APA VPN Events
Cisco Switch Events
SonicWall
SonicWall VPN Events
SonicWall DHCP Events
SonicWall Content Filter Events
Sophos
Sophos All Events
Sophos Content Filter Events
Sophos Firewall Traffic Events
MSSQL Server
MSSQL Server All Events
You can browse these report blocks and select any report that you wish to see. After clicking on a report, you should see an interface like Figure 2.
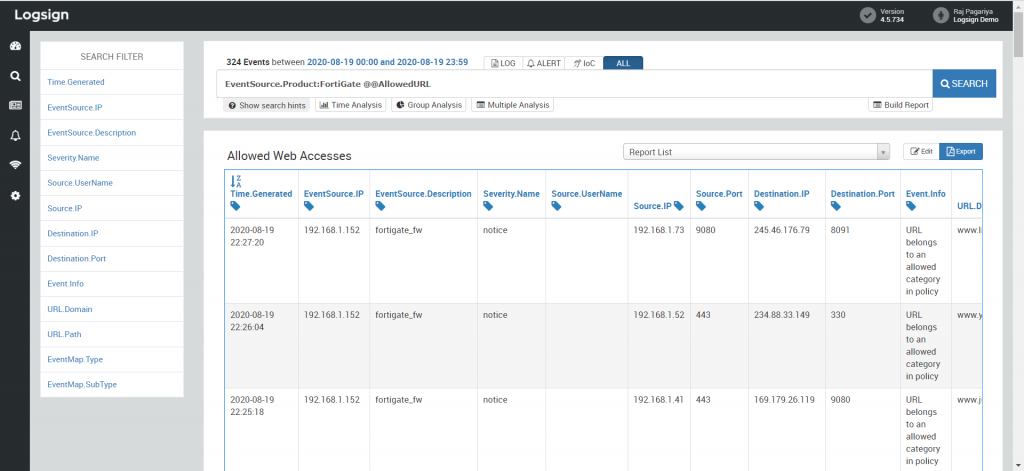
Figure 2: Results for the selected report
The Show search hints button will assist you in further diversifying the results for your report.
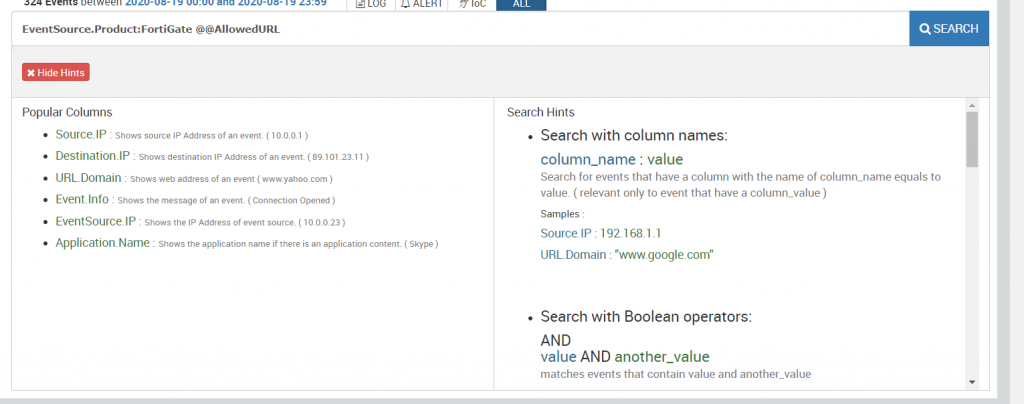
Figure 3: Search hints
For the available data, you can also perform time analysis and group analysis. To perform complex analysis operations, you can explore the Multiple Analysis feature.
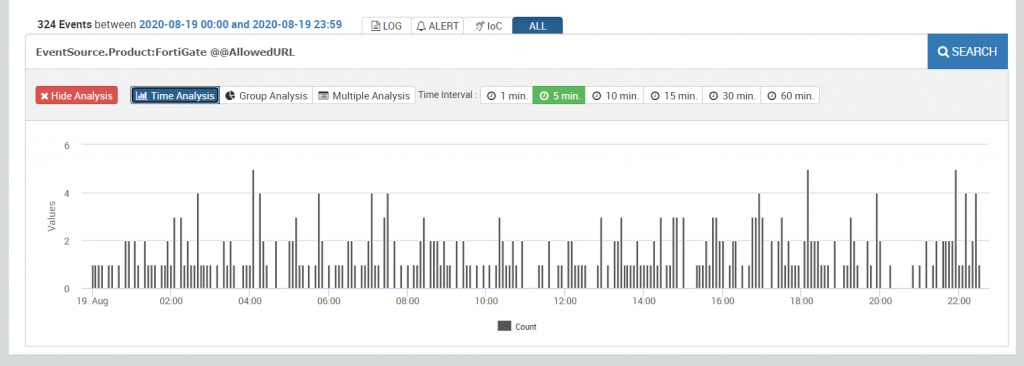
Figure 4: Time Analysis
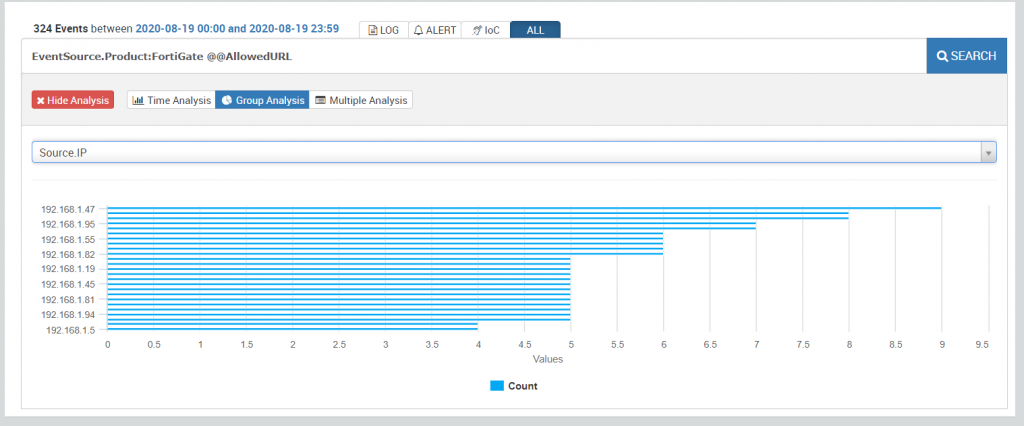
Figure 5: Group Analysis
Using the Export button, you can export the results into formats such as HTML, Excel, and PDF. Based on the type of data in your report, file formats are available.
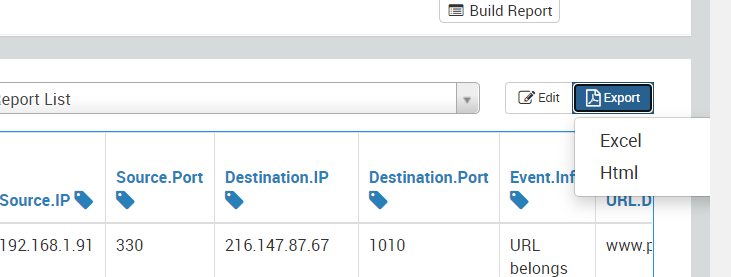
Figure 6: Exporting the report
Now, you will be redirected to the Exported Reports section where you will see all the reports you have extracted so far. Click on the download icon to download your current report.
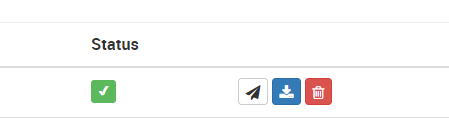
Figure 7: Downloading a report
Have you been able to access the required reports for your company? If not, get in touch with our support team today.
Recommended Reading: What are the types of dashboards in a SIEM solution?