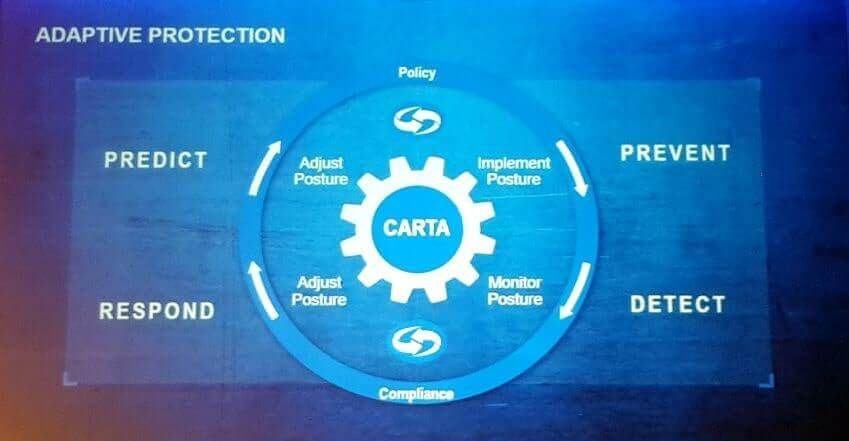
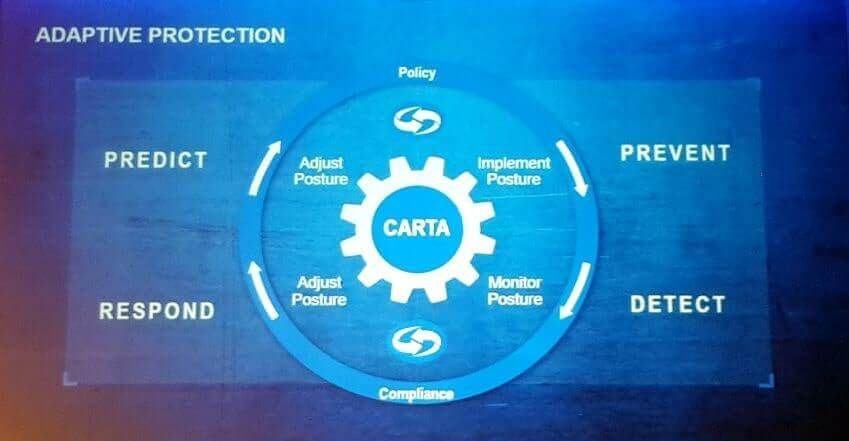
Three stages of IT security where you can implement CARTA (Continuous Adaptive Risk and Trust Assessment): Run, Plan, Build
CARTA (Continuous Adaptive Risk and Trust Assessment) is a novel and efficient approach to the IT security that aims to offer additional context for the cybersecurity professionals when they are making a decision. Keep reading to learn more!
CARTA (Continuous Adaptive Risk and Trust Assessment) was introduced in 2017 by Gartner. Being around for only 3 years, CARTA offers a strategic and efficient approach to the IT security. It is built on the already existing Adaptive Security Architecture by Gartner in order to offer a more thorough protection while keeping up with the most recent developments in the IT environment. In this article, we will take a closer look at what CARTA is and how you can implement it.
In 2017 Security Summit, Garter first introduced CARTA (Continuous Adaptive Risk and Trust Assessment) with a keynote speech by Ramon Krikken, Neil MacDonald and Eric Ahlm. Shortly after, CARTA swiftly and decisively took over the IT security industry. It is a novel and strategic approach that is built on Garter’s already existing Adaptive Security Architecture.
The most important feature of the CARTA is the fact that it pushes the enterprises to employ a continuous, ever-evolving, up-to-date approach to cybersecurity. Because in an increasingly digital business world, we rely heavily on the IT technologies, interconnectedness, the internet itself and cutting-edge connected devices to conduct our business processes. Digitalization and technological advancements offer speed, efficiency and accessibility, but they come with a price: Increased vulnerabilities. That is why a binary approach (black or white, let pass or ban) is far from answering our complicated and very immediate security needs. As a result, organizations and enterprises need to adopt a different approach that allows them to successfully manage risky situations where they cannot see very far ahead or have limited information. The mindset offered by CARTA allows them to make better, more informed decisions based on the degree of trust and gravity of risk.
Key concepts of CARTA can be summarized as follows:
Garter emphasizes that CARTA can be applied in three different phases of the IT: Run, plan and build.
RUN: In the run phase, enterprises make use of analytics to determine a baseline and detect anomalies. With the automated solutions for this phase, such evaluations can be done much more often and successfully. As a result, the organization can notice and respond security incidents significantly sooner.
BUILD: Today, almost all organizations make use of public libraries to create efficient, custom and up-to-date cybersecurity solutions. As CARTA dictates, organizations must carefully analyse these libraries for security risks before implementing them.
PLANNING: Organizations must consider their priorities, assets and value of these assets before implementing IT security solutions. They must plan their budget and roadmap in order to make better decisions along the way.