Data Management on Logsign SIEM: What you must know
Log data plays an unparalleled role in the operation and functioning of a SIEM solution. Or in other words, logs are intrinsic for an effective SIEM solution. Without incoming log data from a variety of different sources in your IT infrastructure, a SIEM essentially becomes useless. In our previous posts, we have explored a variety of features of Logsign SIEM concerning dashboards, reports, search queries, alerts, and behavior definitions. In this article, we explore data management on Logsign SIEM.
If you go to the Settings section on Logsign SIEM, you should see the following options:
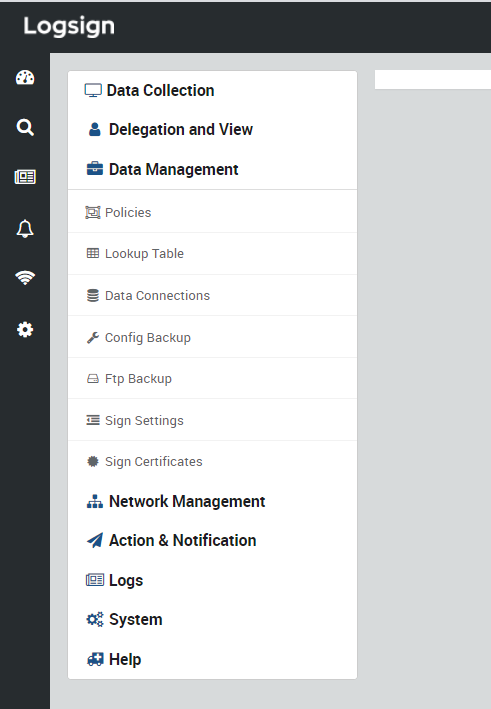
Figure 1: Settings on Logsign SIEM
Each of these options has operations and features available for users. Data Collection covers Source List, Agent Configuration, User Credentials, Data Policies, Log Capture Tool, EPS Stats, Source Stats, Demo Mode, and Update Library. We will be covering Data Collection in one of our upcoming articles. As shown in Figure 1, Data Management has the following options that we will discuss one-by-one:
In this section, you can configure the following:
i. General: EPS (event per second) limit, Rsync client IP, and the percentage of disk usage after which log data should not be recorded. For example, as shown in Figure 2, the SIEM platform is supposed to stop logging when the current disk usage is 90% of the total space available.
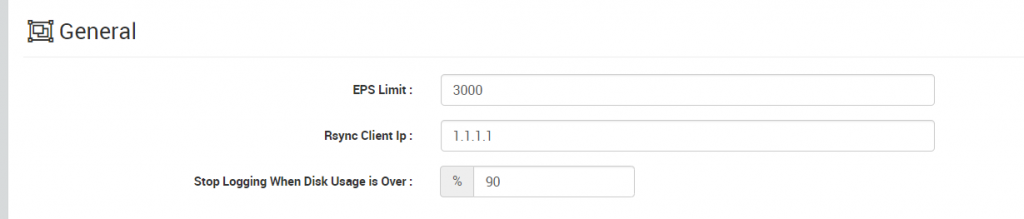
Figure 2: General Policies
ii. Persist Policy: Compression for raw and JSON, persist rotate period, and persist by source address. Apart from choosing either of Bzip or Gzip for compression, you can also choose not to compress your data.
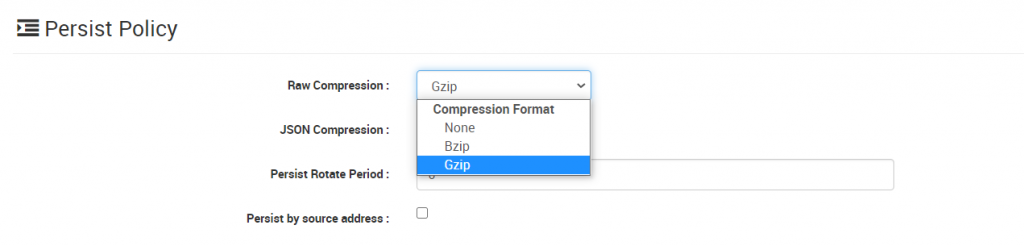
Figure 3: Persist Policy
iii. Service Policy: Checkboxes for Geo IP lookup, reputation service, and details column.
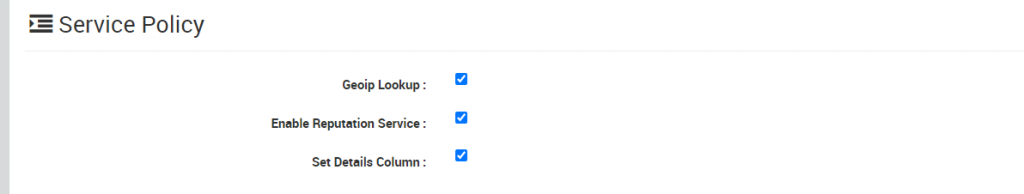
Figure 4: Service Policy
iv. Index Policy: Index Shard Count and Index Replica Count for Captive, Logsign Events, Positions, and Sample, along with Index Merge Factor, Index Refresh Interval, and query preference for search and reporting.
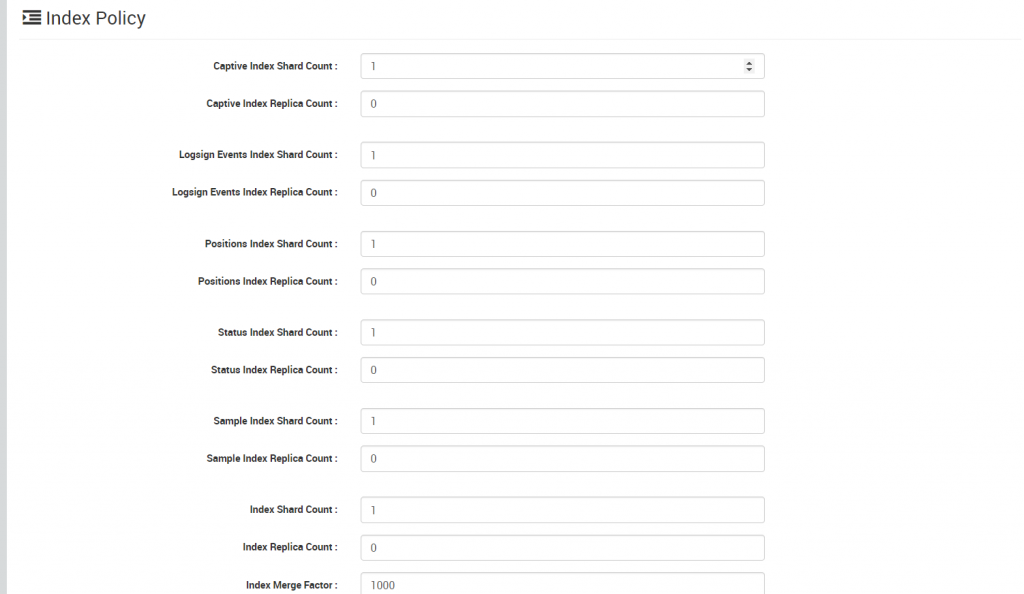
Figure 5: Index Policy
v. Co-Managed Policy: Checkbox for enabling co-management of your organization’s security posture over Logsign SIEM.
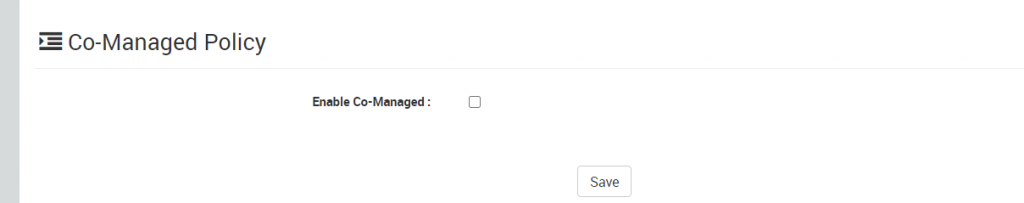
Figure 6: Co-Managed Policy
Logsign SIEM uses lookup tables to enrich information in raw data tables using correlation. For example, a lookup table contains IP addresses with their corresponding geographical addresses. This table can be used to add geographical information to a raw data table containing IP addresses when a query is executed. While using lookup tables, the actual data is never modified. The lookup table on Logsign SIEM consists of the following columns: Source.IP, Source.Username, Source.DisplayName, Source.MAC, and Source.HostName. For the lookup table to function, you must add WMI source, DHCP source, and LDAP connection.
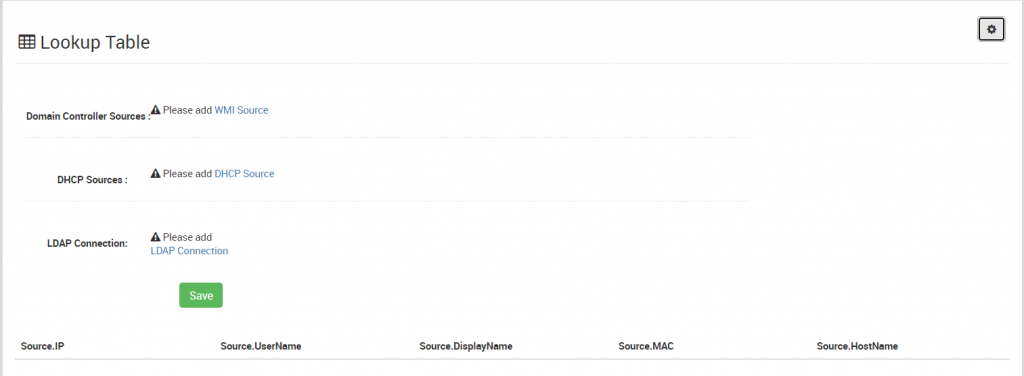
Figure 7: Lookup Table
This section lists data connections for your organization. To add a new connection, click on the Add Connection button and enter the required details: type, description, host, port, database name/SID, username, password, and connect as.
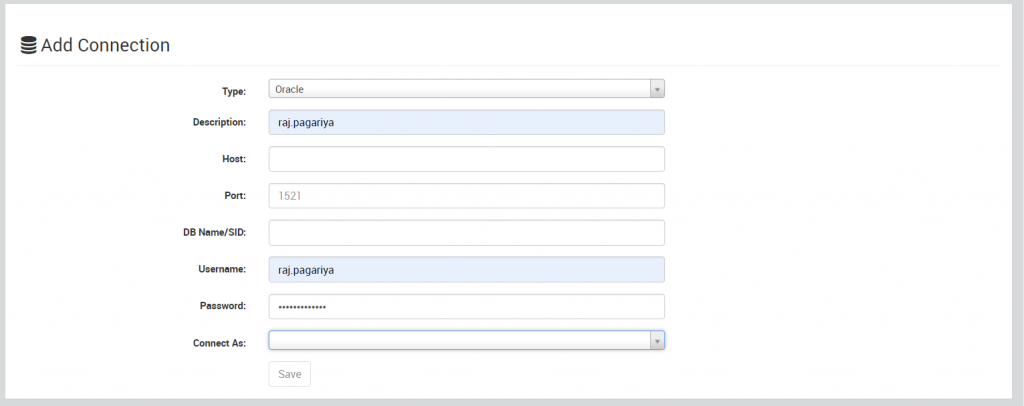
Figure 8: Adding a new data connection
From this section, you can import or export configuration backup files with (.enc) file formats. Logsign SIEM uses this file format to prevent unauthorized access to file contents and prevent their copying.
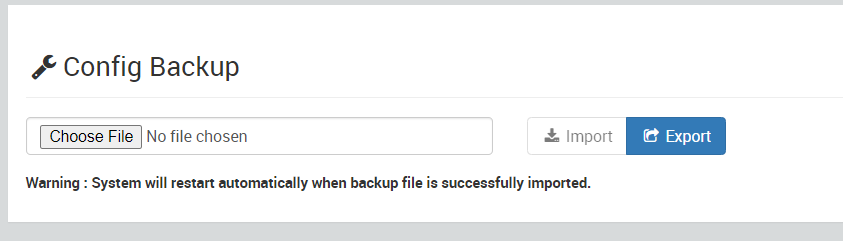
Figure 9: Config Backup
This section directly loads a configuration panel for FTP settings. It requests information such as host, username, password, port, and destination directory. It has checkboxes for active, saving archives, saving signed logs, and creating directories permissions. If you are setting up FTP backup, you can test before saving the configuration settings.
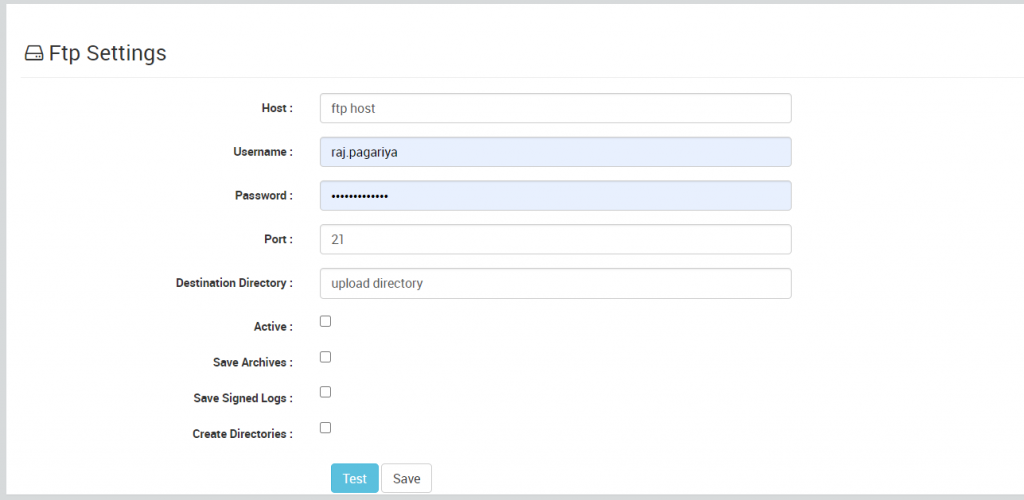
Figure 10: FTP Settings
In this section, you can manage signature settings for data. For File and Summary Sign Methods, you can choose from:
For Line Sign Method, you can select any one from CRC32, MD5, SHA1, and SHA256. For offset hash, you can set it as disabled or choose from MD5, SHA1, and SHA256.
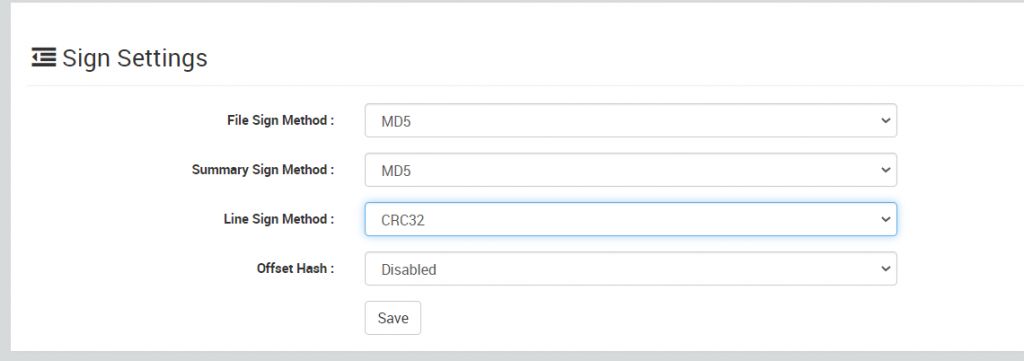
Figure 11: Sign Settings
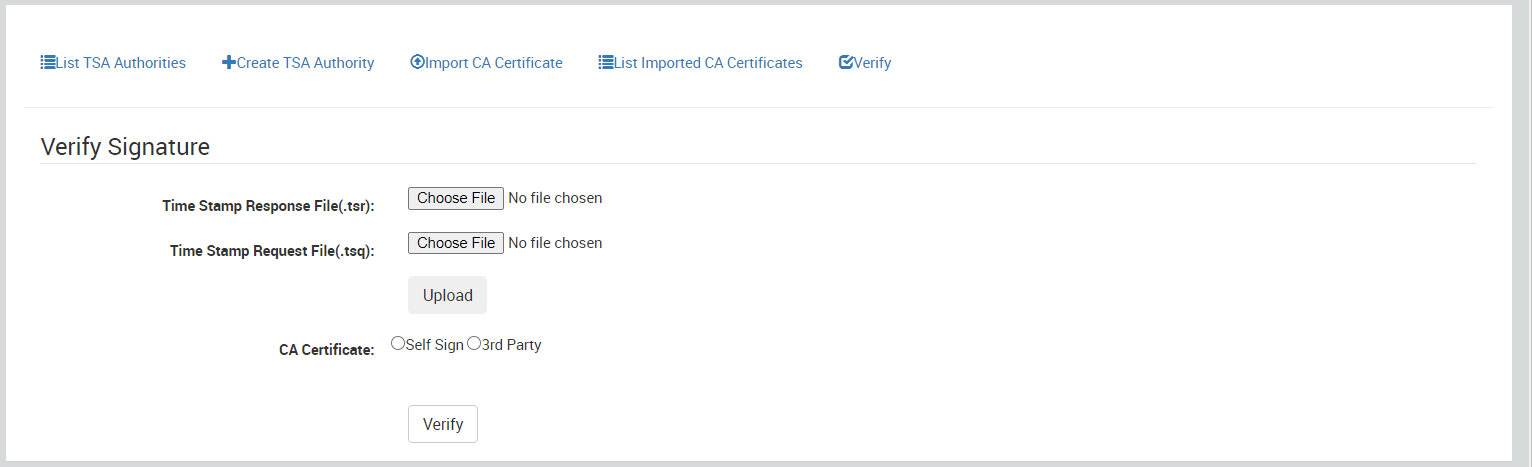
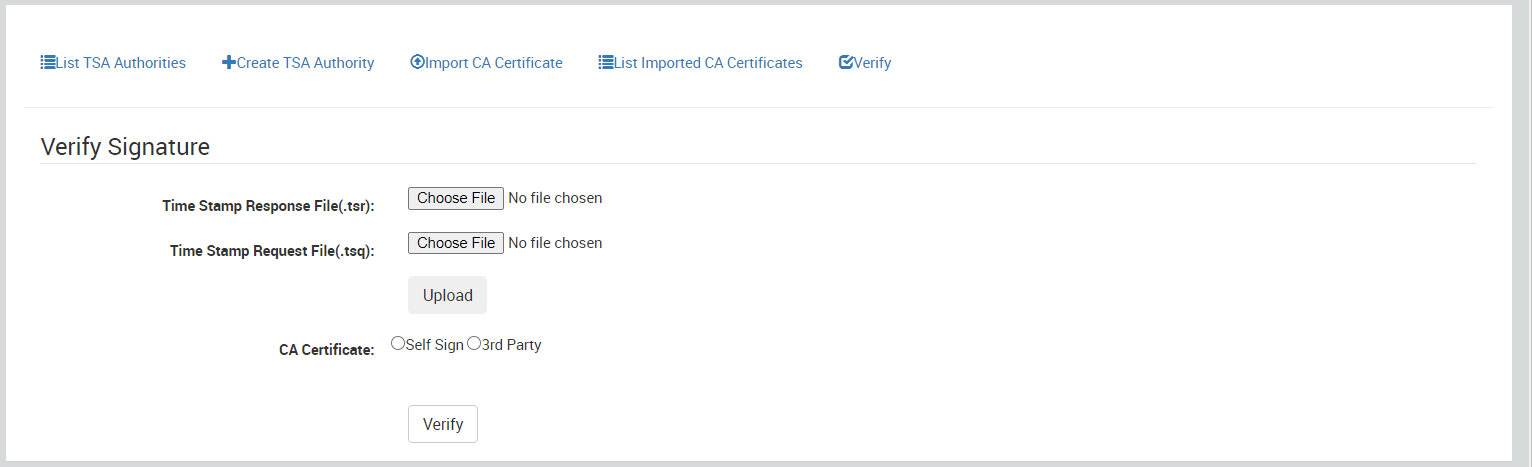
This section helps you in managing signature certificates. Here, you can:
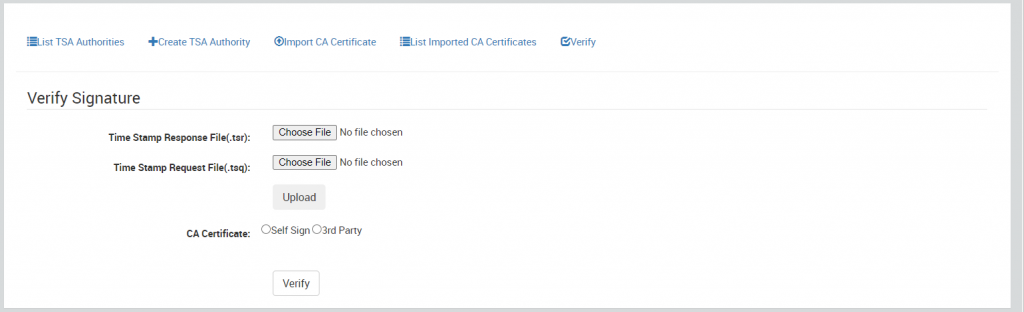
Figure 12: Verifying a signature in the Sign Certificates section (Data Management)
Have you explored the Data Management section for your company? Our support team is always ready to help you with doubts and answer your queries.