Must-Have Features of a Modern SIEM


Initially, Security Information and Event Management (SIEM) solutions were readily adopted because of their capability to provide actionable insights into the deep corners of an organization’s network. Legacy SIEM systems helped in understanding when and where security incidents are happening in real-time. Soon enough, these SIEM systems faced an avalanche of false positives, and they required a dedicated team to filter out irrelevant alerts.
Following this, we saw the emergence of next-generation SIEM solutions that provide functionalities and features that were not available with legacy or first-generation SIEM solutions. In this article, we demonstrate the features of a modern, next-gen SIEM solution.
Back in the day when legacy SIEMs dominated the market, platforms such as Hadoop and Mongo did not exist. Given the amount of data collected and processed by a SIEM platform for a large number of clients, a scalable big data architecture is required. Logsign SIEM is supported by a massively parallelized architecture which remains continuously active with zero performance loss. It provides petabyte level big data experience with unlimited scalability, log retention, storage, and number of users. You can download the Logsign SIEM datasheet to check the details.
In 2020, threats can span across multiple data sources. Ideally, a SIEM solution should collect data from every available source and process it for correlation and analysis. Generally, sources of data include cloud data, network data, log data, etc. Your SIEM should support data management from a single point of control.
Logsign SIEM has a dedicated section for data collection and management in the Settings panel. It collects log data from every possible environment and injects quickly into the SIEM platform. It parses unstructured data with the help of free plugin services and providers real-time super enrichment for threat intelligence and vulnerability assessment. Logsign SIEM allows you to extract and control your security data with a flexible data policy manager.
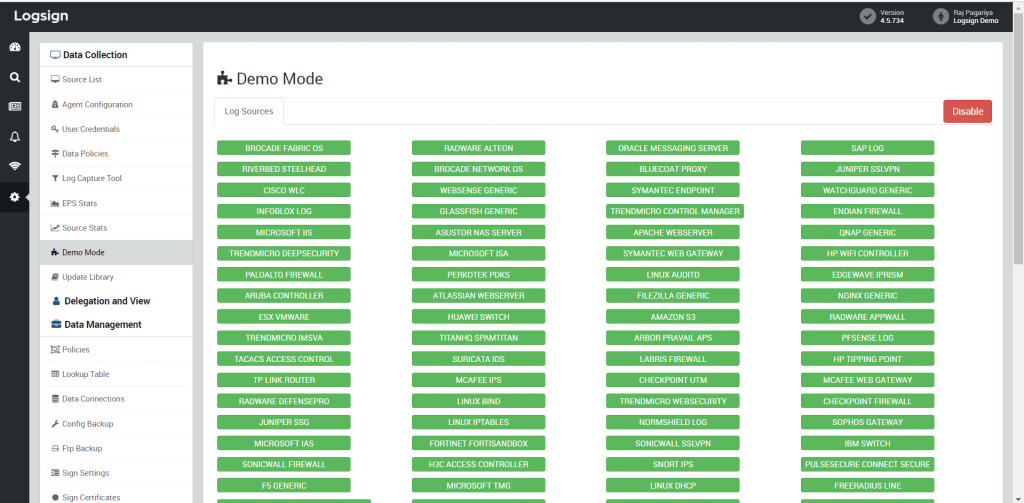
Figure 1: Dedicated section for data collection/management
Logsign SIEM has extensive dashboard management features for your organization to utilize. Coming with over 40+ preconfigured dashboards arranged in 11 categories, Logsign streamlines gaining detailed insights into your organization’s security posture in a few clicks. The SIEM platform relies on state-of-the-art data visualization techniques to make it easier for your team to understand the analyzed data.

Figure 2: A vendor-specific dashboard on Logsign
After your data is collected, you should expect your SIEM solution to provide a high level of enrichment for yielding useful results from the collected data. For example,
Legacy SIEM relied on a security model that focussed on discrete events. However, next-gen SIEMs like Logsign SIEM have turned the tables and enabled advanced analysis of security events. Effective organization of information about each incident helps your security experts to understand the full context in minimum possible time. Utilizing Logsign’s big data platform in line with high-performance search results, threat hunting enables your security team in investigating abnormal behaviours in your IT infrastructure.
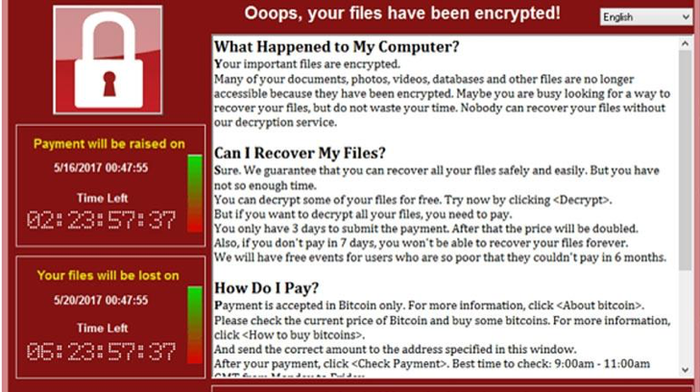
Figure 3: User and Asset Context on Logsign SIEM
Statistics show that a majority of successful cyber attacks involve lateral movement in the network. Put simply; the attackers attempt to gain access to higher privileges or evade detection by changing IP addresses, credentials, etc. A SIEM solution must be able to follow and track lateral movements right from the start to the end.
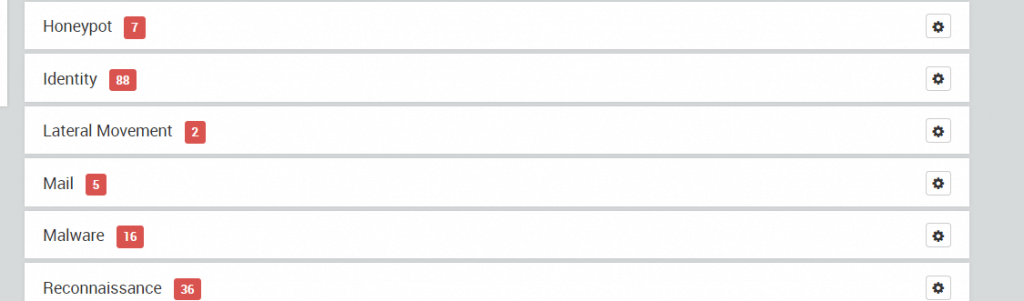
Figure 4: Logsign SIEM consists of a full-fledged use case for tracking lateral movement
Your SIEM may record more than hundreds of thousands of log entries in a week or a month. An ideal SIEM should eliminate false positives effectively and present events with high or critical risk for robust security, efficient team performance, and reduced costs. Alerts are color-coded on Logsign SIEM to enable your security team to filter through high-risk or critical events quickly. Features like these contribute in early detection of security events and provide your team with advanced investigation capabilities.
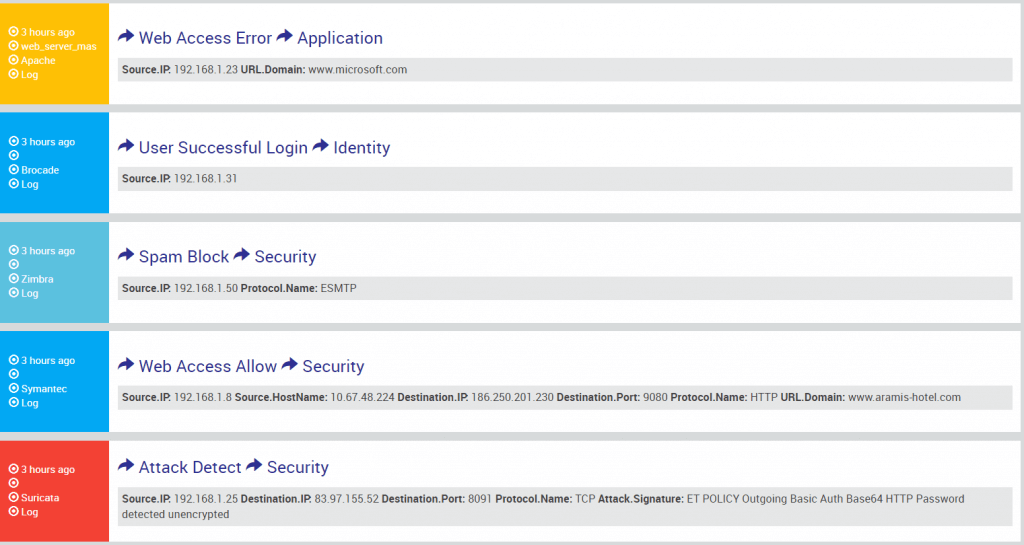
Figure 5: Alerts on SIEM
For a modern SIEM to support user and entity behaviour analysis (UEBA), it requires to understand what normal behavior looks like. Subsequently, using behavioral modeling, statistical analysis, and machine learning, it can identify unusual or abnormal behavior.
As soon as unusual activity is detected, it assigns a risk score and generates an alert for activities that exceed the well-defined threshold.
For example, there is a user on the Logsign network who usually logs in from our Istanbul office. If the same user logs in from Russia or China, such a login will be detected as unusual.
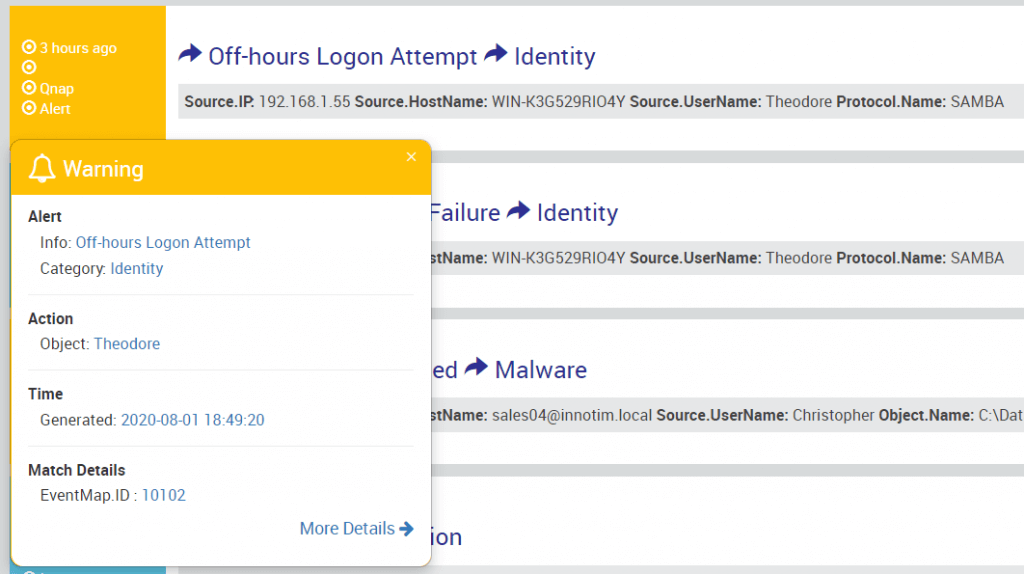
Figure 6: Login outside working hours detected on Logsign platform
A SIEM solution continuously monitors incoming log data from your organization’s technical infrastructure in real-time. Logsign SIEM looks out for malicious behaviour and abnormal activity, and as soon as either one is detected, it alerts your security team with relevant actionable information. Using these alerts, your security team can mitigate security incidents before they turn into an impactful data breach.
Different SIEM vendors use different terminologies or acronyms for this capability of a SIEM solution; however, SOAR is generally preferred over others. Our SOAR offering brings people, process, and technology together. While it can function as a standalone tool, our SIEM platform integrates seamlessly. A SOAR platform allows you to take response and mitigation within your technical infrastructure to a single workbench. It helps your team in creating a coherent security ecosystem, automating repetitive tasks, tracking and prioritizing incidents, driving auto-documentation and communication, increased knowledge sharing among team members, and standardizing workflows.
We understand that SIEM costs are hard to calculate. To make it easier for our prospective customers, we provide multiple pricing methods based on log sources and EPS. At times, it may not be practical for you to visualize your EPS requirements for the future and accordingly, you can choose the log sources based pricing model. Logsign SIEM has a flexible yet easy-to-understand pricing model so that you do not need to cherry-pick your data sources.