What is ICMP?
Being a supporting protocol in the Internet protocol suite, ICMP is often preferred by network devices to send error messages and similar information. Keep reading to learn more!
In order to maintain the security and safety of networks, maintaining a successful communication between devices is essential. That is why protocols like ICMP are very important and popular as of today. In this article, we will discuss what ICMP is and why you need it.
What is ICMP?
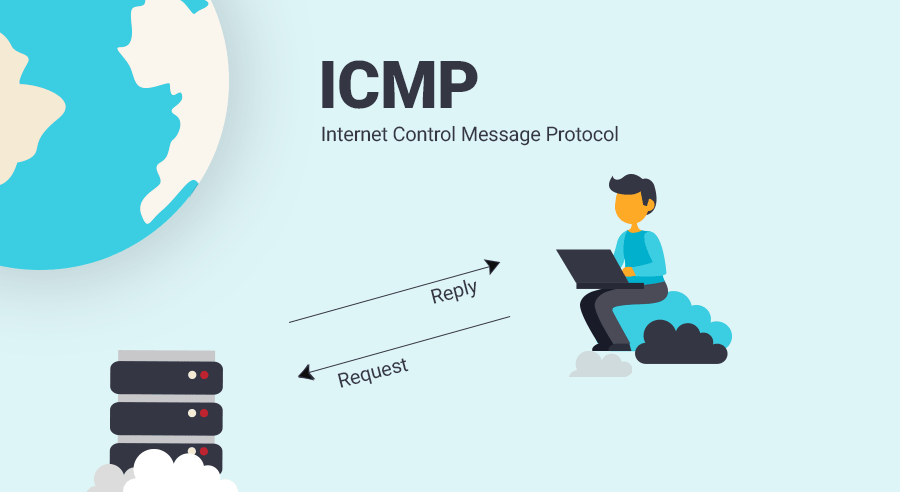
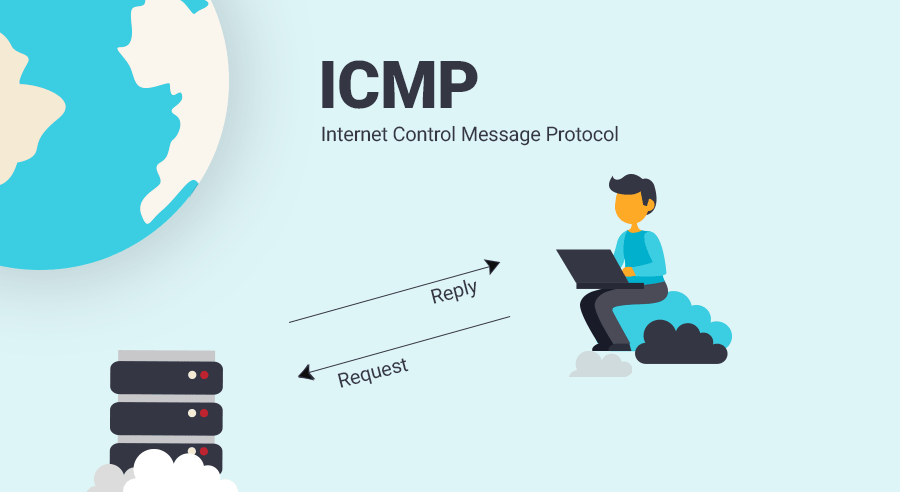
ICMP (Internet Control Message Protocol) is a transport level protocol. Simply put, it is a supporting layer protocol in the Internet protocol suite. The very first definition of the ICMP was penned by Jon Postel who is considered as one of the founding fathers of the Internet. The original definition of the ICMP has been altered several times and the latest description of ICMP is specified in RFC 792 in detail. This latest description was published in September 1981.
ICMP is stacked on the Internet Layer and supports the core Internet protocol. It is considered as one of the most essential systems that allow the internet to work flawlessly.
What is the purpose of ICMP?
IP does not have a built-in mechanism that sends control messages and error messages. That is why a protocol like ICMP is needed. Practically, ICMP offers error control and often it is employed to report errors, send management queries and operations information.
Network devices like routers need to use the ICMP in order to send the error messages. That is why ICMP is considered as a supporting protocol.
It is a known fact that the lower Internet Layer does not need to be concerned with assuring the connection, yet ICMP is very much needed for important feedback when things go out of order.
What are the ICMP message codes?
ICMP offers feedback and information regarding errors, control messages and management queries. The first code field in the ICMP block singlehandedly manages to convey a great deal of information. Below you can find some of the most relevant values the first code field can have and their meaning:
0: Echo Reply. It is used for ping.
3: Destination is unreachable.
4: Source quench. It means that the router is overloaded.
5: Redirect. It denotes the use of another router.
8: Echo Request. Similar to 0, it is used for ping.
9: Router advertisement reply.
10: Router solicitation.
11: Time Exceeded. It is used for traceroute.
Smurf attacks and ICMP
Sometimes, equipment owners might prefer turning the ICMP features off. It might sound odd at first since ICMP capabilities provide an important service for the router yet there is a reason behind why people shut ICMP off: Smurf attacks!
Hackers can use ICMP properties in order to conduct a smurf attack. Since smurf attacks employ a reflector strategy, the echo request of the ICMP can be exploited for hacking purposes. The hacker finds their way into the broadcast address on the network and manipulates the system to send out echo requests. As a result, devices on the network replies the host router of that broadcast IP address with an echo.
If you would like to learn how you can protect your organization from hackers and other malicious attackers, get in touch! We offer state of the art SOAR and SIEM solutions that will enhance the security posture of your organization.