Viborot Ransomware: Another Big Nightmare
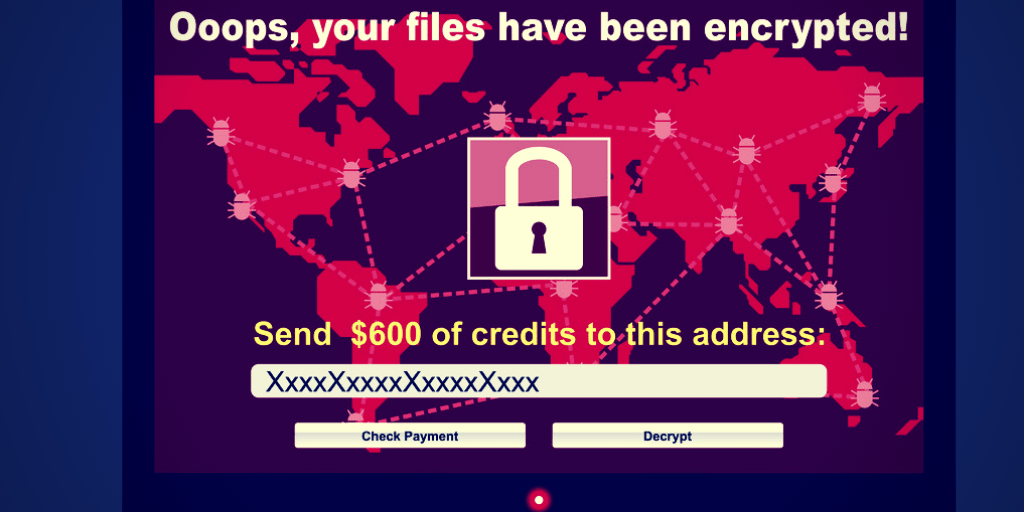
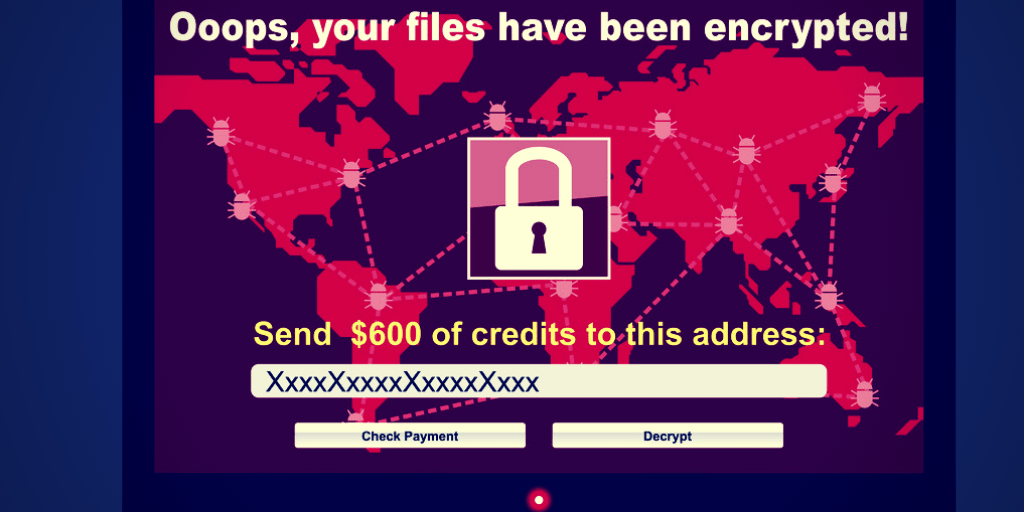
Trend Micro security researchers revealed a new malware which is a multi-tasking threat that includes botnet, ransomware, and keylogging capabilities in a single package. Virobot not only encrypts files on the infected systems but also entangle the machine into a spam botnet and forces it to disseminate itself to other victim machines. Viborot was first discovered on 17 September 2018 and security folks pointed out that it was not associated with any other ransomware family. The threat checks infected systems to verify the existence of particular registry keys (machine GUID and product key) to determine whether the system can be encrypted or not. As a matter of fact, Viborot utilizes a cryptographic Random Number Generator (RNG) to generate the encryption and decryption keys, which is then sent along with the machine-gathered data to Command and Control (C&C) server via the POST. For encryption purposes, the malware attacks file types such as .html, .odt, .xml, .psd, .php, .asp, .sql, .mdb, .jpg, .png, .csv, .xlsx, .txt, .docx, and numerous others. Once the attack is successfully launched, the ransomware shows a ransom note on the ransom screen. According to the Trend Micro, the ransom note is displayed in French, but the main focus of the attack is the United States. Furthermore, Viborot’s keylogging feature collects keystrokes and downloads additional files from the C&C server. Reads the analysis published by Trend Micro, “Viborot also has a keylogging feature and connects back to its C&C server to send logged keystrokes from an infected machine. Once connected to the C&C, it may download files – possibly another malware binary – and execute it using PowerShell.” Viborot employs the Microsoft Outlook of the compromised machine to implement the spam botnet capability and disseminate it to the victim’s contact list. After that, the malware is attached to the victim’s contact list or an infected file or the Virobot will send a malicious file downloaded from its C&C server. During the analysis of Viborot, this ransomware does not encrypt any files since the C&C server temporarily taken down, security researchers revealed. As a result, it can be realized that ransomware attacks are growing by leaps and bounds. Viborot is the most recent example of the ransomware’s menace. However, organizations’ defensive mechanisms are not as good as they should be. The main reason behind the poor security posture is the use of ineffective security program. The smart choice of the security program is indispensable. For instance, Logsign’s SIEM system is one of the most reliable and effective security solutions for organizations. As a final remark, Trend Micro suggests enterprises that “Individuals and enterprises should use a multi-layered approach to mitigate the risks brought by threats like ransomware.”