Arbor Pravail Availability Protection System (APS) Integration
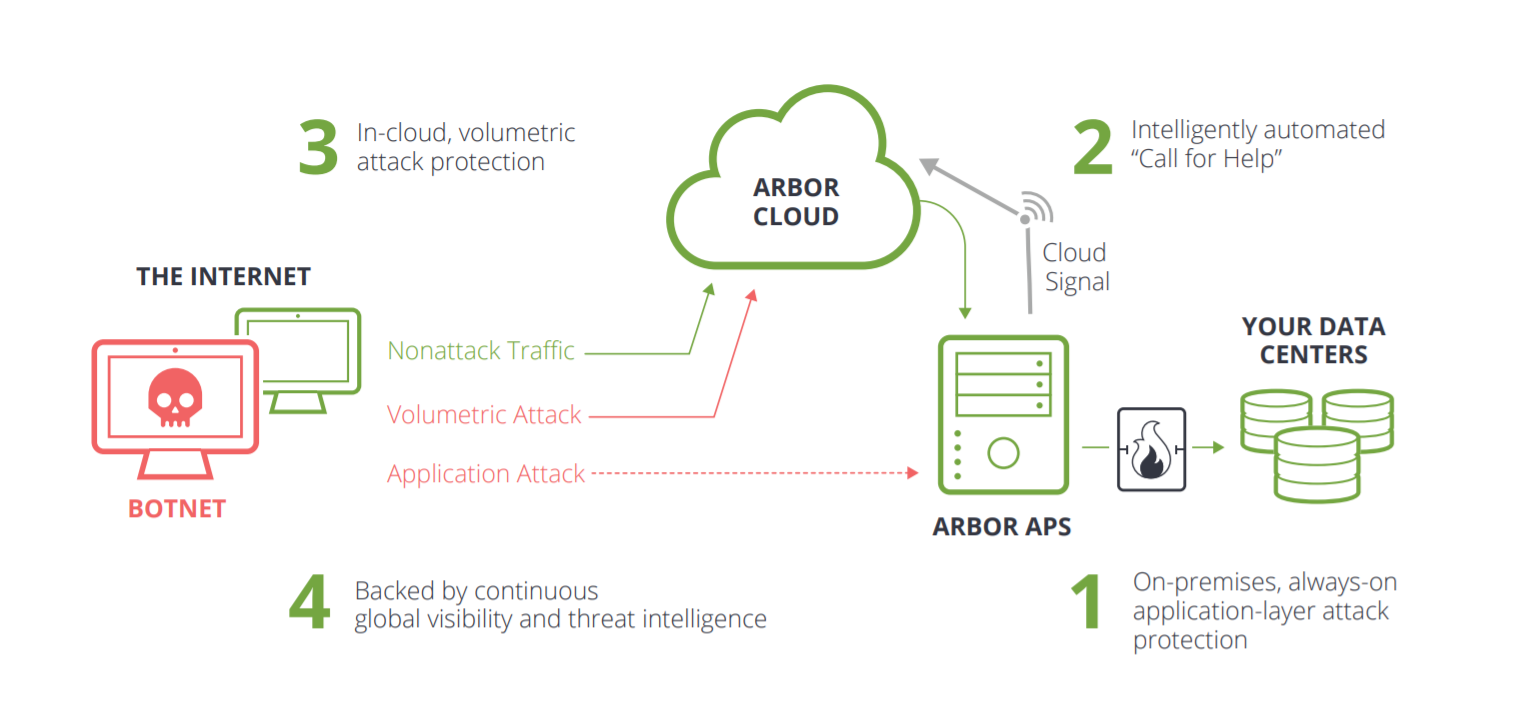
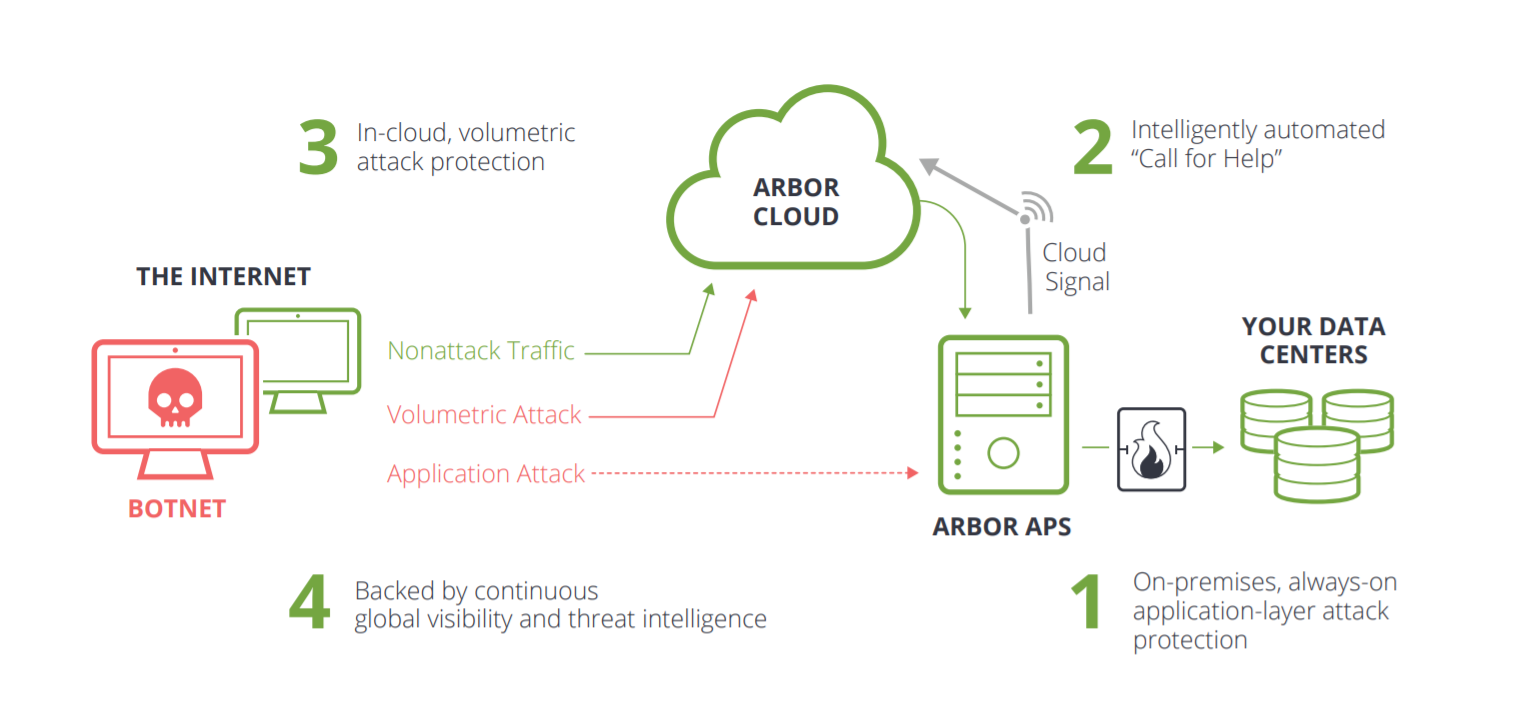
The global spread of botnets (collections of compromised computers) has led to an epidemic of DDoS attacks. As attack tools become more sophisticated and easier to use, botnet operators are bringing down targeted applications with low bandwidth attacks that escape detection both in provider networks and by traditional perimeter security devices. Data center operators are typically unaware of such attacks until critical services are down or badly degraded. At that point, there can be extreme pressure to find and fix the problem. Yet the tools and expertise to do so are often lacking. Arbor APS enhances your overall protection by using Cloud Signaling™ to intelligently and automatically connect local protection with cloud-based DDoS services. With Cloud Signaling, APS automatically alerts upstream service providers, such as your ISP or Arbor CloudSM, when larger attacks threaten availability. This allows for a faster time to mitigate attacks. [Figure 1]
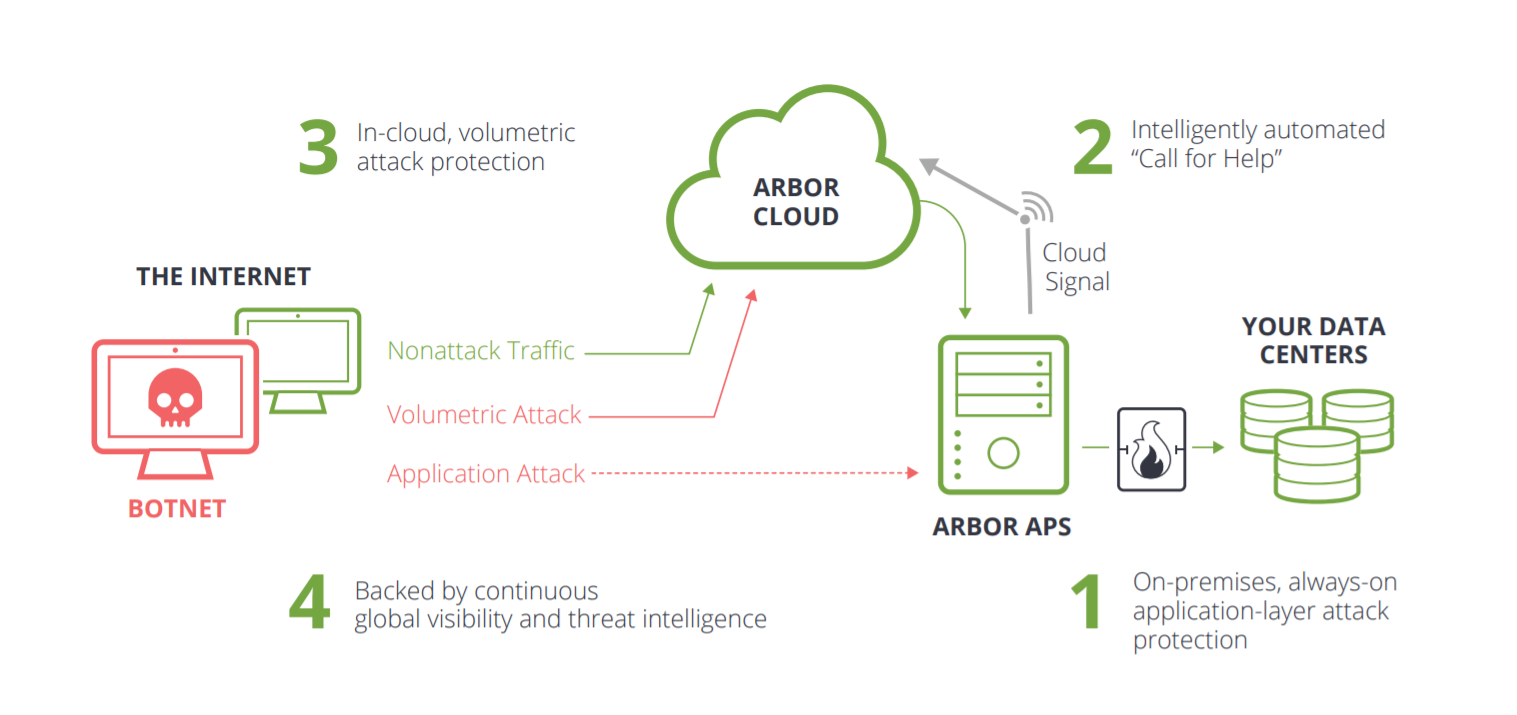 Figure 1: The fully integrated combination of 1) APS on premises for always on, in-line protection against application-layer attacks; 2) Intelligent Cloud Signaling to 3) Arbor Cloud to stop the larger attacks — 4) all continuously armed with the global threat intelligence of ATLAS/ASERT — offers the most comprehensive DDoS protection solution in the industry.
Figure 1: The fully integrated combination of 1) APS on premises for always on, in-line protection against application-layer attacks; 2) Intelligent Cloud Signaling to 3) Arbor Cloud to stop the larger attacks — 4) all continuously armed with the global threat intelligence of ATLAS/ASERT — offers the most comprehensive DDoS protection solution in the industry.Event Types Event types detected by Arbor APS can also be monitored real-time from the dashboard and report on Logsign. In addition any type of event can be monitored in detail.[Figure 2]
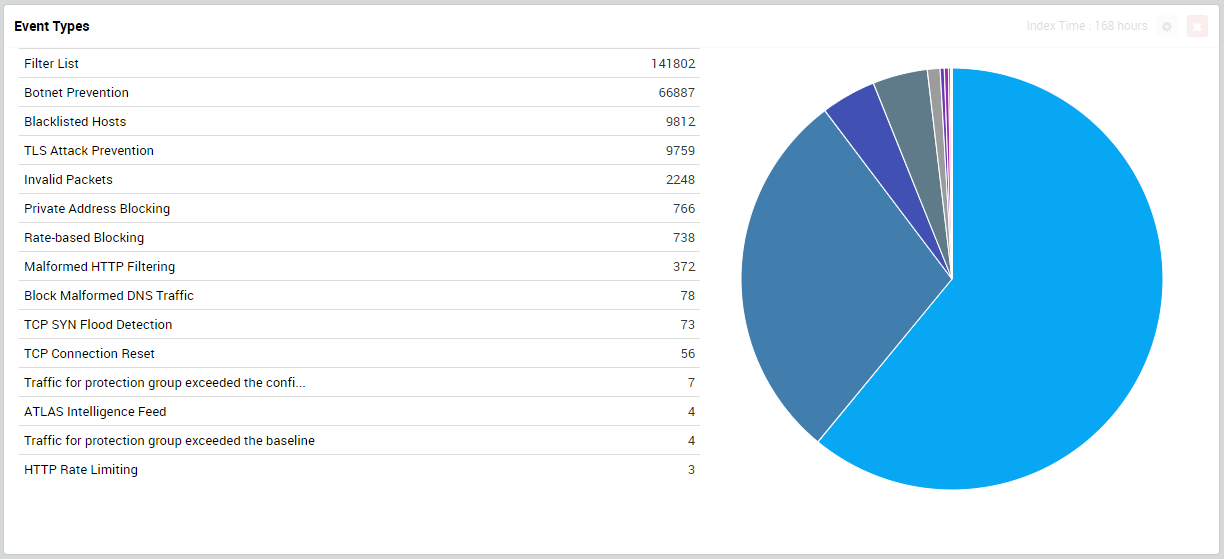 Figure 2: Events detected by ARBOR.
Figure 2: Events detected by ARBOR.Country Detection with GeoIP Location Sources and destination IPs detected by Arbor APS can be identified by Logsign GeoIP service, and monitored real-time from the dashboard and report.[Figure 3]
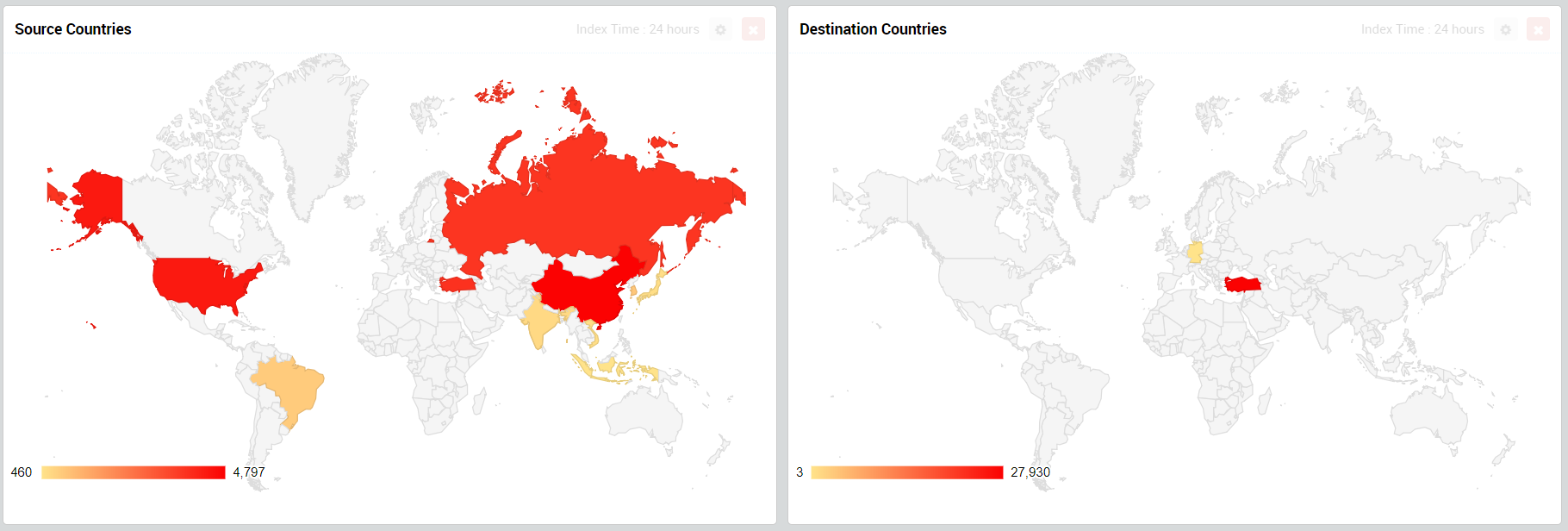 Figure 3: Source & Destination Countries.
Figure 3: Source & Destination Countries.Services & Protocols The services and protocols identified by Arbor APS can be actively monitored by using dashboard, and in addition, unknown services and protocols can be analyzed and identified on Logsign. [Figure 4]
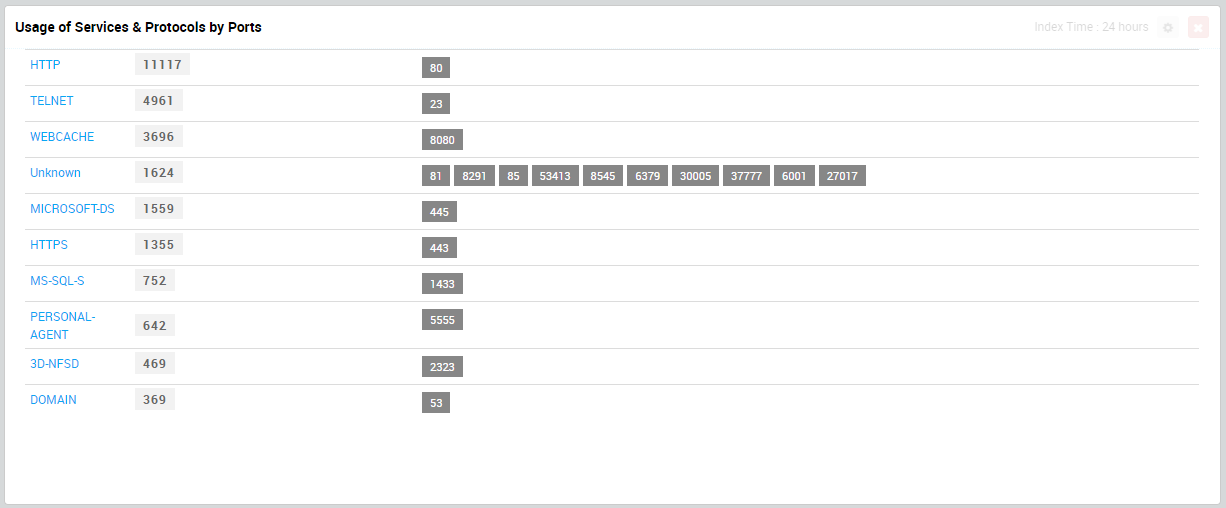 Figure 4: Service & Protocols
Figure 4: Service & ProtocolsSecurity Events & Activities by Time The events identified by Arbor APS can be monitored actively and instantly by using dashboard. [Figure 5]
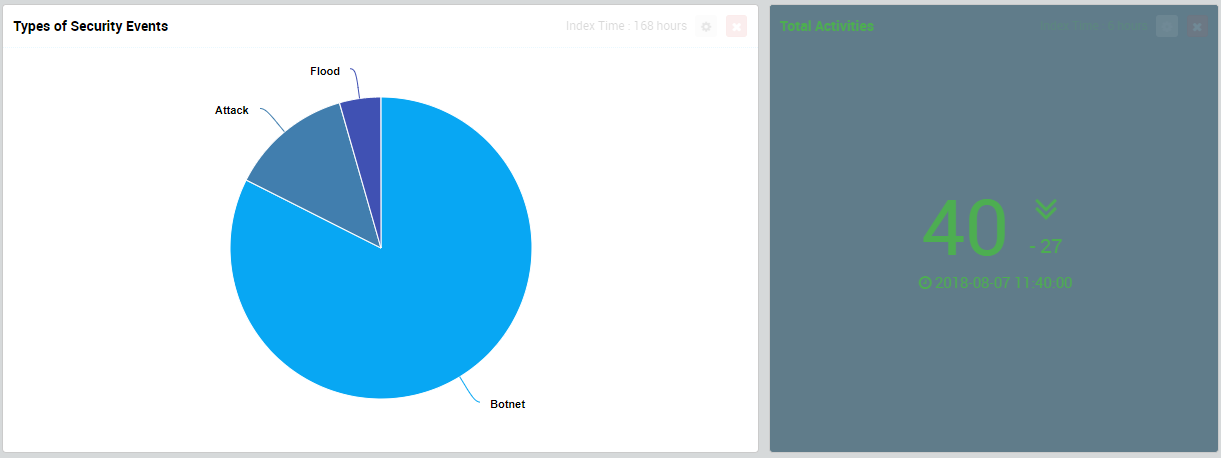 Figure 5:Security Events
Figure 5:Security Events