Developing security monitoring use cases for SIEM
At Logsign, we believe that every one of our clients faces a unique set of threats. There can be overlapping; however, it would be highly rare that two organizations face the same set of threats. Accordingly, when you are using a SIEM solution like Logsign SIEM, there will be use cases that are more important to your business than others. If you have used a SIEM tool previously, you know that a SIEM is a powerful tool to identify the smallest of threats in your entire technical infrastructure. However, for this to happen, use cases should be correctly defined and searched in the right location.
Logsign SIEM already features various inbuilt use cases for your organization to utilize. Before you start working on building new use cases, you must focus on three essential components: insights, supporting data, and analytics. Senior team members of your organization’s security team should define the use cases. These use cases can be justified with supporting data and analytics. For example, insights can be the presence of malware, abnormal behavior of a user, or validation of your organization’s security controls. Sources of data can be network packets, threat intelligence feeds, business context, events, and logs. On the other hand, analytics will include machine learning, rule-based systems, pattern matching, and behavior analysis.
Your first step should focus on listing the required data points for your use case. As we have seen while designing inbuilt use cases on Logsign SIEM, most of these data points will be the logs from your IT infrastructure. For advanced analytics involving human experts, internal policies and procedures, along with HR documents, may be useful. For better understanding, you can also check the available data sources on Logsign SIEM.
Figure 1: Data sources on Logsign SIEM
The second step is about choosing the correct data analysis techniques for your use case. While creating a use case on Logsign SIEM, you will encounter multiple instances where you will need to select various data operations such as:
First, while defining a new behavior;
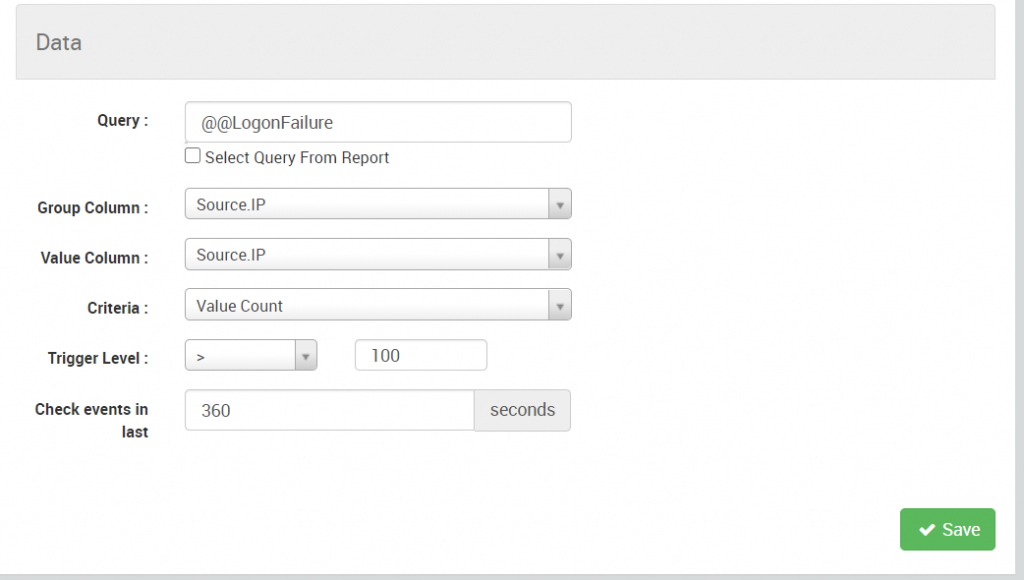
Figure 2: Defining a new behavior
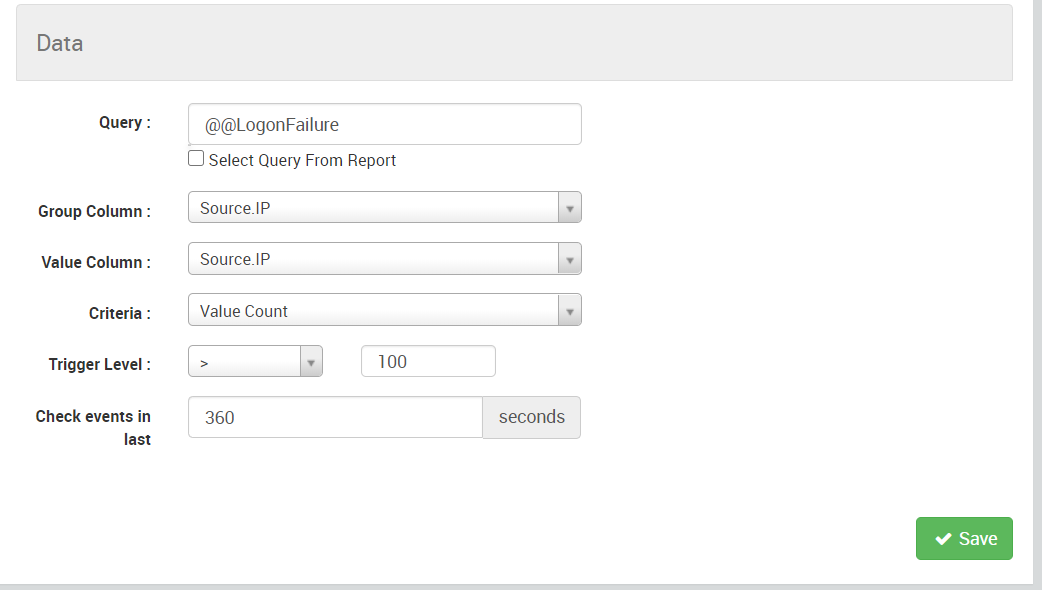
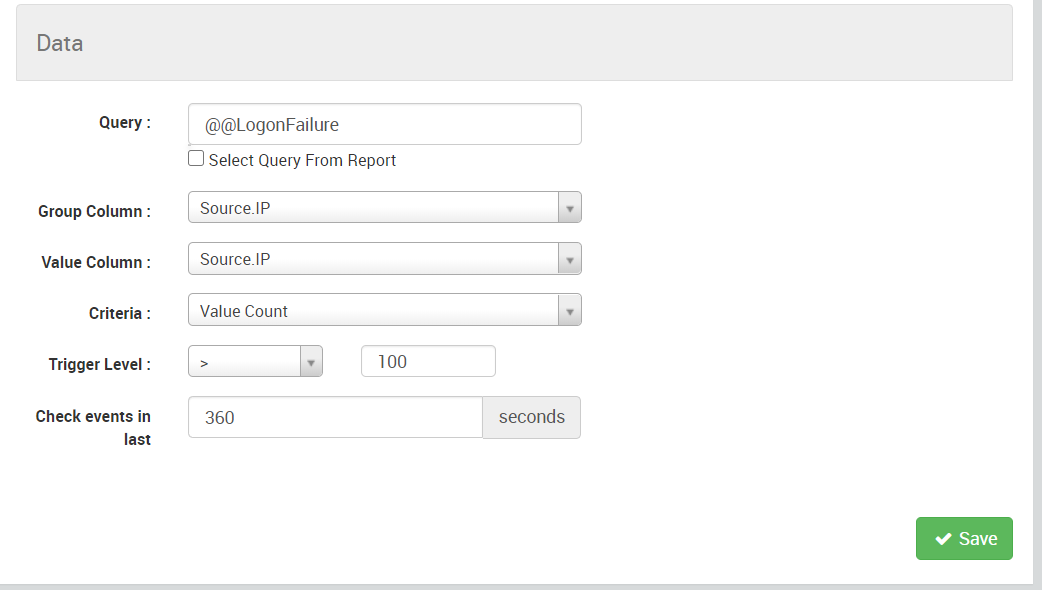
Second, while creating a new rule;
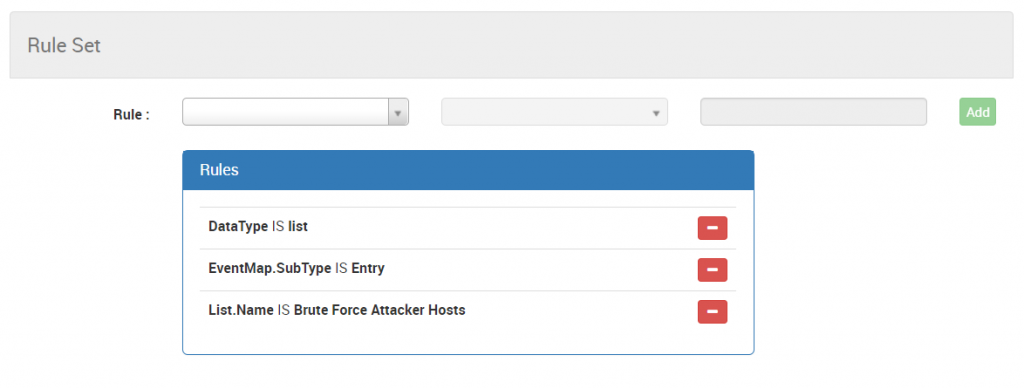
Figure 3: Creating a new rule
Third, while defining report parameters; and so on.
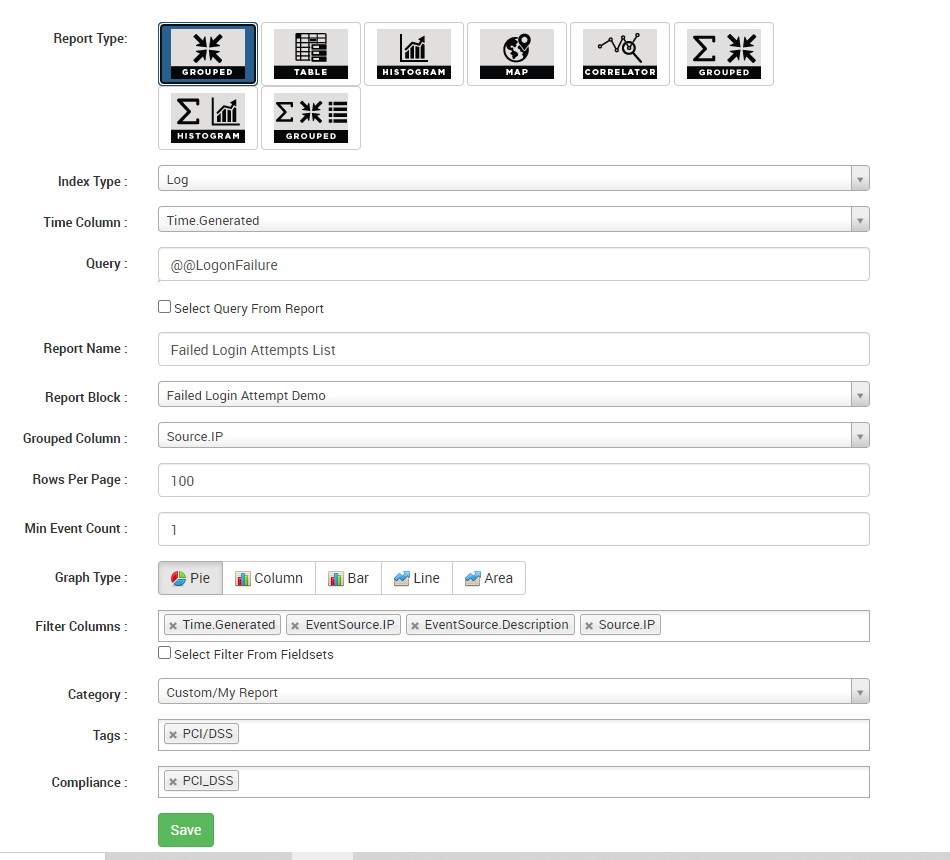
Figure 4: Defining new report parameters
Apart from these basic operations, you can always get in touch with our support team to understand how advanced data analytics works on Logsign SIEM. Here, you must note that there can be multiple overlapping methods for data analytics, and at times, it is possible to achieve overall results by combining several simple techniques. Our experts recommend that for any given use case, you should select the most straightforward data analysis technique. The apparent benefits of this approach include "easy to understand" techniques for your team and quicker fine-tuning or modifications as needed.
Over the years, while defining use cases, we have learned that:
A use case made today may be irrelevant a couple of years down the line. Each use case on your SIEM platform would have its lifecycle in our ever-evolving cyberspace. This is precisely why you should designate team members to optimize and review your existing use cases aggressively. Over time, you may create new use cases that will overlap with older use cases. As a result, the SIEM platform can generate multiple alerts and increased false positives/negatives. Once you decide that a particular SIEM is not relevant any more, you should deprecate it and perform a clean-up exercise on your Logsign platform.
Are you struggling with creating your organization-specific use cases? Get in touch with our Support team today.