How to Check the Integrity of a File?
In the world of cyber warfare, the internet has become a vital part of every walk of life. When it comes to downloading a file from the internet to your laptop or PC, you cannot be guaranteed a 100% safety due to the existence of fast and sophisticated cyber threats. Security vulnerabilities, data breaches, viruses, and malware have become very common and result in exploitation of the originality, integrity, and authenticity of any file you download from the internet.
It is essential to verify the authenticity of a file to avoid incidences of downloading suspicious data and infecting your computer with ransomware, viruses, malware and other corrupt and harmful malicious components. One compromised file, even of a few bytes, can exploit the company’s entire IT infrastructure if it is not being detected and eradicated altogether.
Checking the integrity or hash value of a file is aims at checking that either a file is genuine or verifying that a file has not been modified by untrusted parties. Checking file integrity is vital for both individuals and organizations.
Every single file on the internet is unique in its way and when it is changed or altered, either its hash value or its digital signature change. Therefore, analysts can use both digital signatures and hash values to check the integrity of a file.
To ensure the integrity of a file, some websites display MD5 value near the download link of a file or a program (See Figure 1 Below).
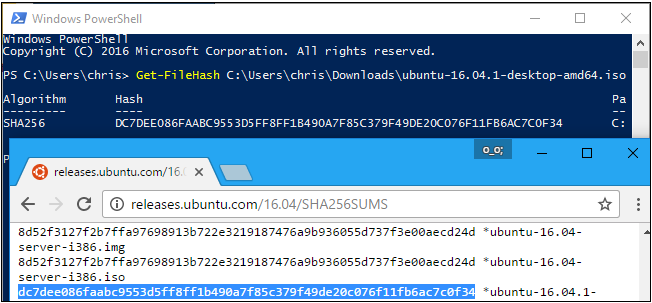
Figure 1: MD5 Value Along with a File
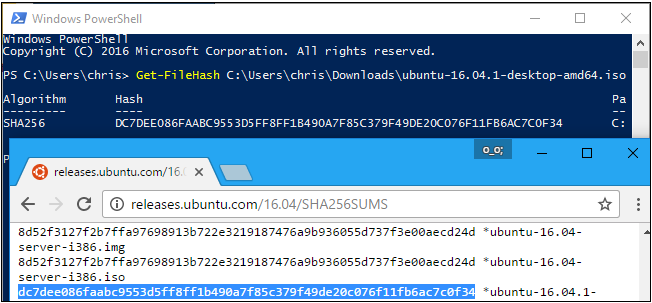
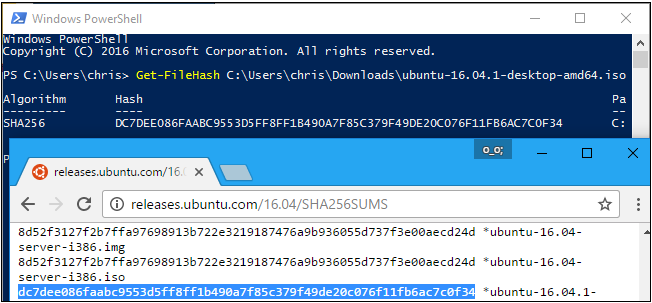
MD5 or SHA family hashes are set of random strings that allow security professionals to make sure that the downloading file is not tampered with or not corrupted. Some operating systems such as Linux, MacOS, and Windows allow verification of downloaded files through their hashes. For example, Windows OS offers Windows PowerShell to do this.
In fact, every file has a unique data. The analysts apply a Cryptographic Hash Function to check the hash value of a program. This function verifies whether the file is in the current state or it has been modified by malicious actors. Cryptographic Hash Function algorithm works by comparing the file’s original and current hash values. And if a byte or even a piece of the file’s data has been changed, the original and current hash values will be different, and therefore you will know whether it’s the same file or not.
The most popular used algorithms on the website are SHA1 and MD5 hash values. To be able to check the integrity of a given file, you only need a utility tool or a third party. The commonly used third-party utility is:
This is one of the most efficient and most effective third-party utility program used to check the hash value of a file (See Figure 2 below).
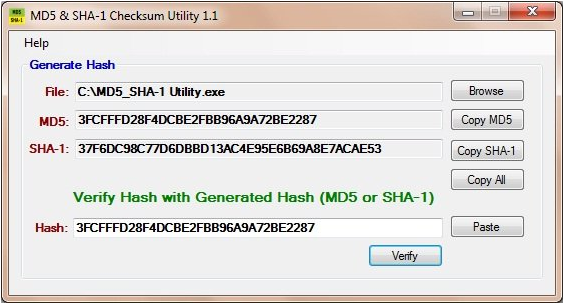
Figure 2: MD5 & SHA-1 Checksum Utility 1.1
It is an easy-to-use application whose premise is straightforward. On downloading and installing the MD5 and SHA-1 Checksum Utility, in the front of the File Field, you click on Browse (See the above Picture). After that, you need to select the file that you want its hash values generated and open it. Also, you can drag and drop the file onto the MD5 and SHA-1 Checksum Utility. On giving the program a file to check its hash values, in a matter of no time, the MD5 and SHA-1 hash values are generated.
Unlike other programs that seem to be bloated, MD5 & SHA-1 Checksum Utility gives hash values with no frills making it a complete freeware that is compatible with Windows 7, Vista and XP.
As a result, it has been realized that checking file integrity is crucial to thwarting the penetration of cyber pests through a porous hole provided by malicious files. Therefore, it is vital to check the integrity of the file before downloading it to your PC, laptop, or any other device. The unauthentic file can result in the spread of Ransomware, Malware, Spyware, and other viruses.